The GDPR, Collecting Personal Data, and Updating Your Privacy Policy

The European General Data Protection Regulation, or GDPR, entered the scene in May of 2018 with the purpose of protecting the personal data of users and reducing the risk of security breaches and mishandling of personal data on the internet.
Before the GDPR came into effect, many companies would collect and store as much personal data as possible and keep it forever. Now, though, companies can't keep or use any personal data unless they have the users' consent or another legal basis to do so.
We'll take a look at how the GDPR affects the collecting of personal data, and how this in turn affects your Privacy Policy.
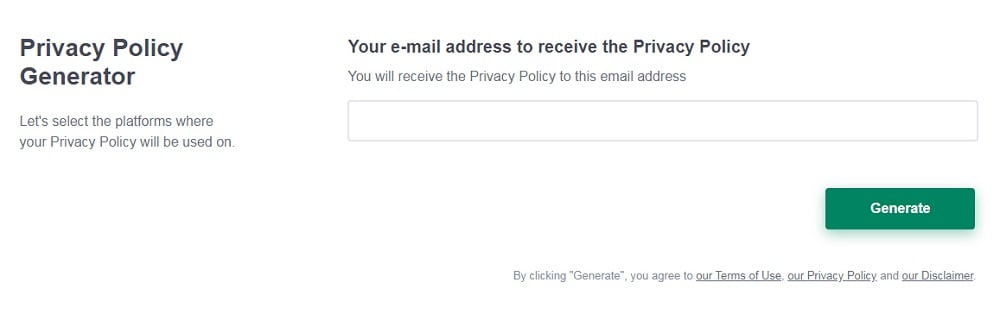
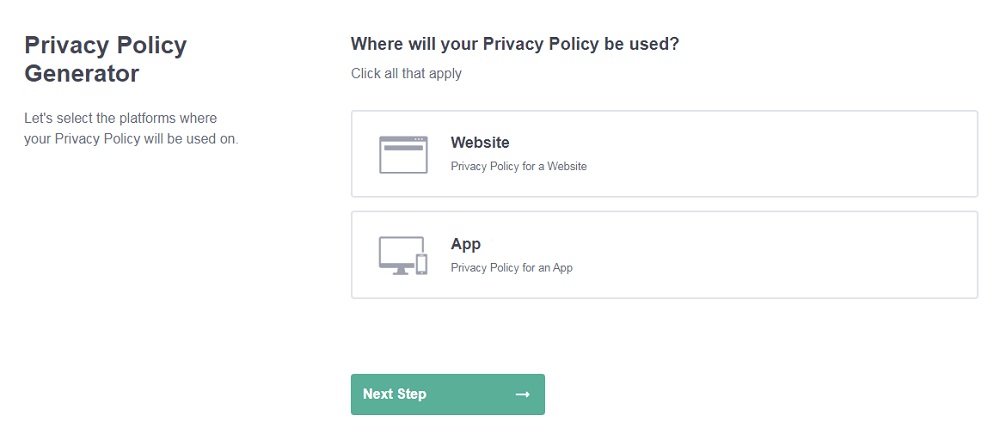
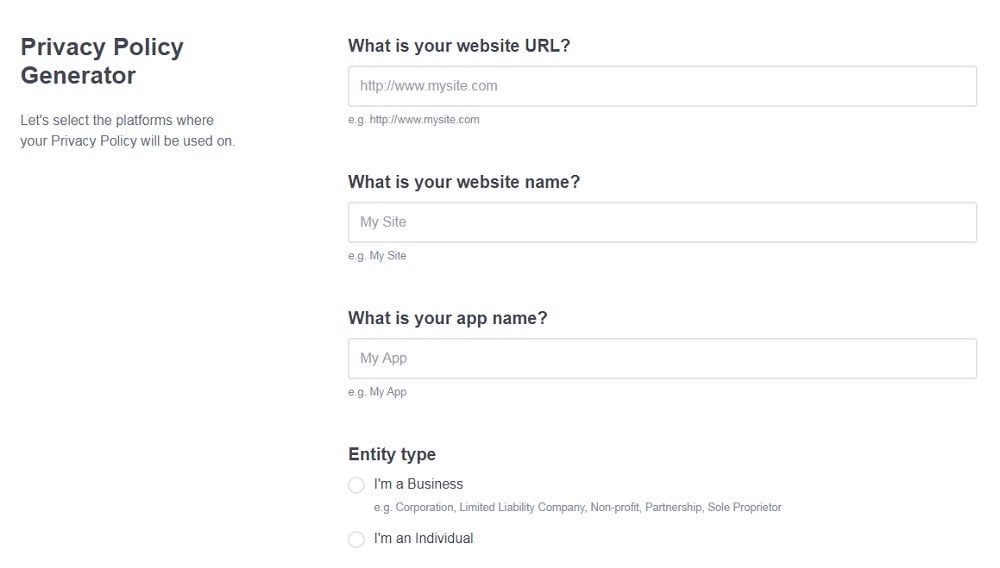
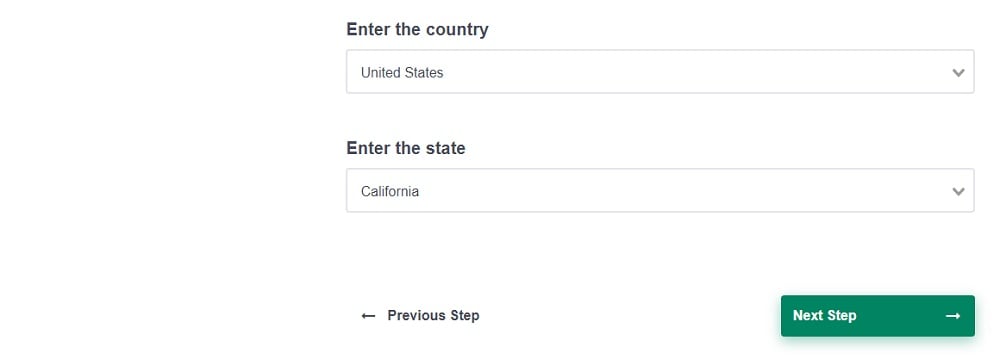
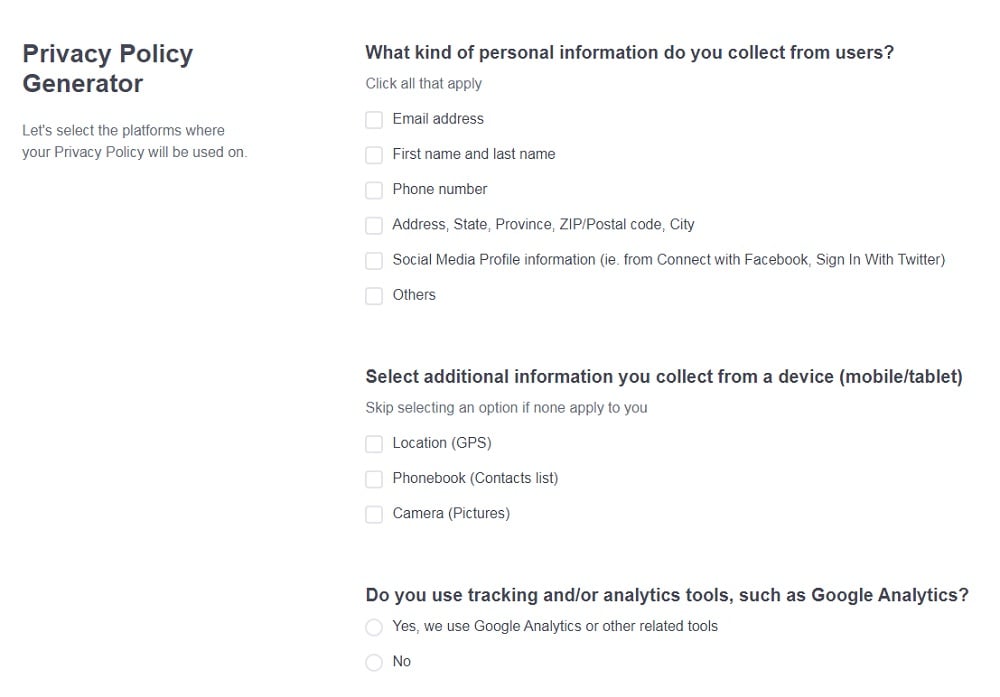
Need a Privacy Policy? Our Privacy Policy Generator will help you create a custom policy that you can use on your website and mobile app. Just follow these few easy steps:
- Click on "Start creating your Privacy Policy" on our website.
- Select the platforms where your Privacy Policy will be used and go to the next step.
- Add information about your business: your website and/or app.
- Select the country:
- Answer the questions from our wizard relating to what type of information you collect from your users.
-
Enter your email address where you'd like your Privacy Policy sent and click "Generate".
And you're done! Now you can copy or link to your hosted Privacy Policy.
- 1. What is Personal Data?
- 2. GDPR Requirements
- 2.1. Controllers, Processors, and Subjects
- 3. Anonymity and Encryption
- 3.1. Anonymization
- 3.2. Encryption
- 4. Legal Bases For Collecting Personal Data
- 4.1. Vital Interests
- 4.2. Public Interests
- 4.3. Contractual Necessity
- 4.4. Compliance with Legal Obligations
- 4.5. Unambiguous Consent
- 4.6. Legitimate Interests
- 5. Privacy Policies
- 6. Steps To Take Now
What is Personal Data?

Personal data includes nearly everything about an online user including:
- Name
- Email address
- Location
- IP address
- Browser history
The GDPR classifies a lot of information contained in web server logs as personal data by default. Web servers like Apache and NGINX automatically collect and store two of these three types of logs:
- Access logs
- Error logs
- Security audit logs
Some sensitive personal data can be logged by accident, like referral information from another website that provides sensitive services.
Personal data can seem abstract and trivial, but a lot of it can be very sensitive and even dangerous if left unsecured.
GDPR Requirements

The GDPR states that you can collect and store certain information as long as the users remain completely anonymous. There can be no chance that the user can be traced from the data you have stored.
The data must be held for the shortest amount of time possible. If the data becomes obsolete or unnecessary, it must be wiped. Your company should set time limits and clearly stated reasons for keeping personal data.
That personal data must always be accurate and up-to-date. For example, if your company collects resumes for recruitment purposes, you can't keep them longer than your clients are unemployed and you must request updates from your clients while you hold their resumes.
According to the GDPR, you should almost never collect certain sensitive data such as:
- Race or ethnic origin
- Political opinions
- Religious or philosophical beliefs
- Trade union memberships
- Genetic or biometric data
- Health or mortality
- Sex life or sexual orientation
Usually you can only collect this data if it's required by law. Make sure to state in your Privacy Policy if you have permission to collect this type of data and why you need it.
Controllers, Processors, and Subjects
GDPR requirements differ slightly between controllers and processors, and all requirements exist to protect subjects.
Controllers are companies and organizations that collect personal data and use it for certain purposes, like a website that markets to users based on their online behavior.
Processors are the middle men who analyze the data and make suggestions on how to use it.
Subjects are the users themselves.
Anonymity and Encryption

Anonymization and pseudonymization methods used to keep an individual's personal data and their identity separate. The difference between anonymization and pseudonymization is whether the data can be linked back to the user.
Anonymization
Anonymization is the complete stripping of identity from personal data. The identifiable information is completely deleted. Nobody, not even the organization who collected the data, can identify the person whose data was collected. Ever.
Pseudonymization is the detachment of data and identity, with one caveat. The data and the individual cannot be reconnected without some extra information held separately from the data.
By doing this, organizations can keep the data safe and use it more liberally then they otherwise could.
Encryption
Encryption is the process of turning personal data into unintelligible information. The data is still there, it just can't be read by humans. It uses algorithms, an encryption key, and a decryption key.
The GDPR doesn't necessarily require encryption. It just vaguely mentions encryption and doesn't suggest any level of encryption, where to use it, or what types of data or processing you should encrypt.
However, it's still useful to understand how it works and how it can change the way you process data.
Data Protection Authorities suggest having a policy in place that states when and when not to use encryption. Encryption is usually used to maintain security and avoid processing that does not comply with the GDPR.
Legal Bases For Collecting Personal Data

There are six legal bases for collecting, holding, and processing data as stated in the GDPR:
- The vital interest of the individual
- The public interest
- Contractual necessity
- Compliance with legal obligations
- Unambiguous consent of the individual
- Legitimate interest of the data controller
Each basis holds the same value, so they are not exclusive to each other. You cannot rely on a single basis if there is a less intrusive way to perform the relative task. Some circumstances may seem to fit one basis, but can better rely on another.
You'll always need to:
- Document the decision to use a basis,
- Specify the task, function, or power, and
- Identify the statutory or common law basis
Vital Interests
You can use vital interest as your legal basis when the collection of someone's data is imperative for protecting their life if they cannot give (or deny) consent. If the person whose data you are collecting is able to give consent, even if they refuse, you can't depend on vital interests.
If you might need to use this basis, prepare to document any circumstances that would make it relevant and make sure you can justify the reasons behind it.
You'll usually need to use vital interests for processing data in a medical emergency where the individual can't consent (or deny consent). Another basis, like legitimate interests or public interest, would be more fitting if that person's medical care has already been arranged.
Using someone's personal data to protect another person under vital interest is rare. However, it can be relevant if you need to use a parent's data to protect their child. Humanitarian emergencies, like an epidemic or natural disaster, can also call for the vital interests basis.
Public Interests
You can rely on public interest when the data is being collecting to inform and protect the public. This basis is usually used for processing the data of:
- Public authorities
- Suspects in criminal cases, local or national
- Employees and their bosses in social security and social protection cases
- People who deal with public and state finances
- Subjects of scientific and historical studies if the processing is necessary for the research
It's mostly relevant for public authorities or anyone who works for the public.
Contractual Necessity
Contractual necessity is appropriate if you need to collect someone's data to enter into or fulfill a contract.
This is relevant if you need to fulfill specific obligations, like processing and delivering an online order. This is also relevant if you need to perform a task before entering into the contract, like providing a quote.
Compliance with Legal Obligations
Compliance with legal obligations is relevant if there is a law requiring a task to be done and that task requires personal data to be collected. Contractual obligations don't count as they have their own basis.
An example of this is an employer who is legally required to report employee salary details to Her Majesty's Revenue and Customs (HMRC) and needs that employee's personal data.
Unambiguous Consent
Unambiguous consent of the individual is applicable when the person whose data is being collected has already given consent for the processing. This means you have to offer the individual real choice and control. They should be in charge of their privacy. This allows for your company and the individual to build trust. It also allows you to enhance your reputation.
The GDPR requires that consent is given via positive opt-in. Never try to deceive users by using pre-ticked boxes or any other form of default consent. Make the options clear and specific.
Tell your users about any third-party controllers who might also rely on their consent. Document the who, when, how, and what of the consent process and keep it as evidence. Public authorities and employers especially need to be able to provide proof of consent and should never rely too heavily on it.
Create a review process for your consent requests and update them when needed. Avoid making consent a precondition to using your services.
Legitimate Interests
Legitimate interests works if the users fully expect their personal data to be processed and the processing has little impact on their privacy. It is the most flexible basis, but not always the most relevant.
In order to rely on this basis, you should:
- Identify a legitimate interest
- Prove the processing is necessary for the service to be done
- Weigh it against the user's rights, freedoms, and interests
If the processing is done at the expense of users' rights or interests, you should consider a different basis.
Public authorities can rely on legitimate interest, but only if it's for tasks performed outside their public duty. Otherwise, they should rely on the public interest basis.
Your company's interests or the interests of a third party can be considered legitimate interests.These can be commercial interests, individual interests, or broader societal benefits.
Keep a record of your legitimate interests assessments (LIA) as proof of compliance. Your legitimate interests should be stated in your Privacy Policy.
Privacy Policies

One of the most important things to do in order to comply with the GDPR is updating your Privacy Policy to fit the requirements. Mostly, you'll just have to make things more specific.
Conduct a privacy law self-audit so you know exactly what privacy practices your business engages in and what information you need to disclose to your users.
Be as clear and transparent as possible. For example, the part of your Privacy Policy that says how you use personal data should also say whether you use the data to make automated decisions and how.
The GDPR also requires that your Privacy Policy be easy to read and understand. Your Privacy Policy is intended for the average user so try to reduce legalese, jargon, and other complicated words as much as possible.
A great example of a clear Privacy Policy with an explanation on how personal data is used is this section from Medium's Privacy Policy:
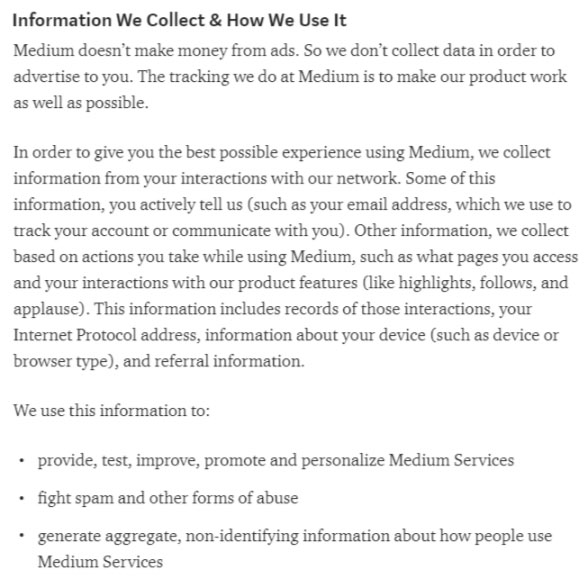
You'll also need to disclose exactly how you and any third parties will use the personal data.
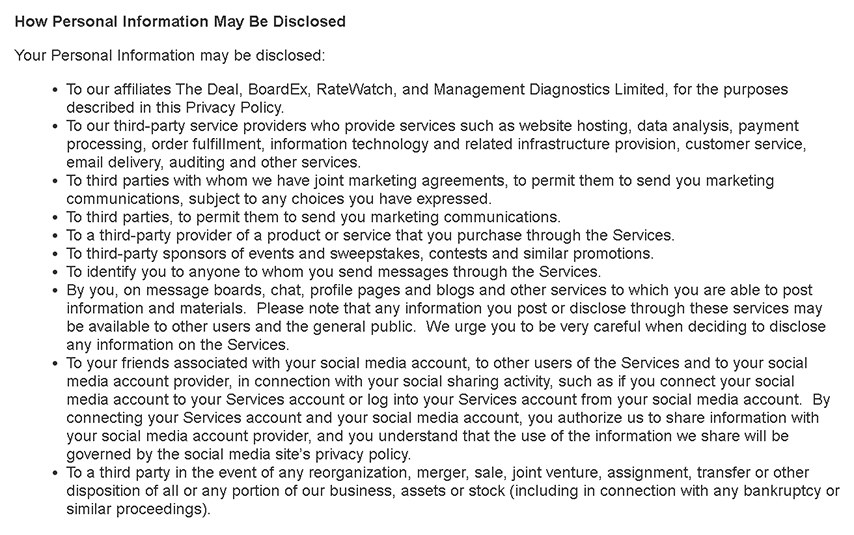
Your Privacy Policy may already say that you share data with third parties, but it should also say who those third parties are. Keep them updated at all times.
TheStreet has a great section on third parties in its Privacy Policy:
Steps To Take Now
Companies, organizations, and other website owners need to be aware of who is visiting their site and what information they are gaining from those visitors. If that information can be categorized as personal data, which it most likely can, website owners need to find a way to protect it.
In order to comply with the GDPR, make sure your users are aware of when, how, and why their personal data is being used. Give them the option to consent unless you have a legal basis for using their data without permission.
Keep your Privacy Policy updated and clear. The average internet browser is not a lawyer or a government authority. They need to know exactly what they are getting into without digging through jargon and legalese. If you make material changes and updates, use a Privacy Policy Update Notice to inform your users of these changes. Chances are you've seen lots of these sent out from other companies about their own updates.
It's extremely important to comply with the GDPR, not only to protect users but also to build trust between them and your company.


