Privacy Law Self-Audit: Protecting and Managing Personal Data

If you run a business and collect visitors' personal data, you must follow various data protection laws. These rules give consumers control over what data they share, who they share it with (e.g. third parties) and how data is used, such as for marketing and analytics data sharing.
We'll give you an overview of what laws you need to be aware of, what they require and how you can meet the requirements at your business. Keep reading and do a self-audit to make sure your privacy practices are up to standards.
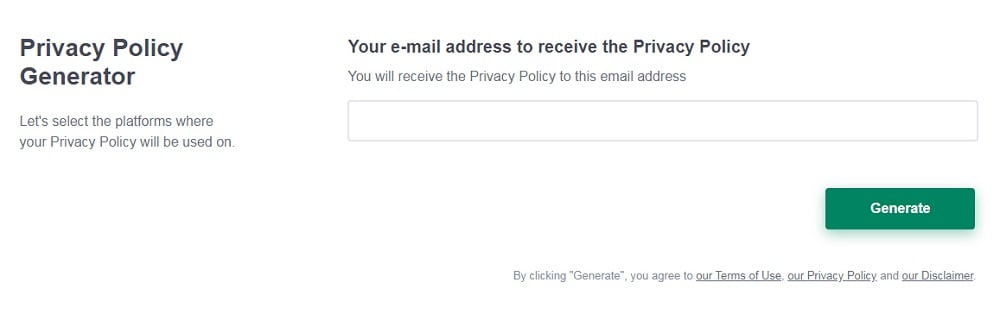
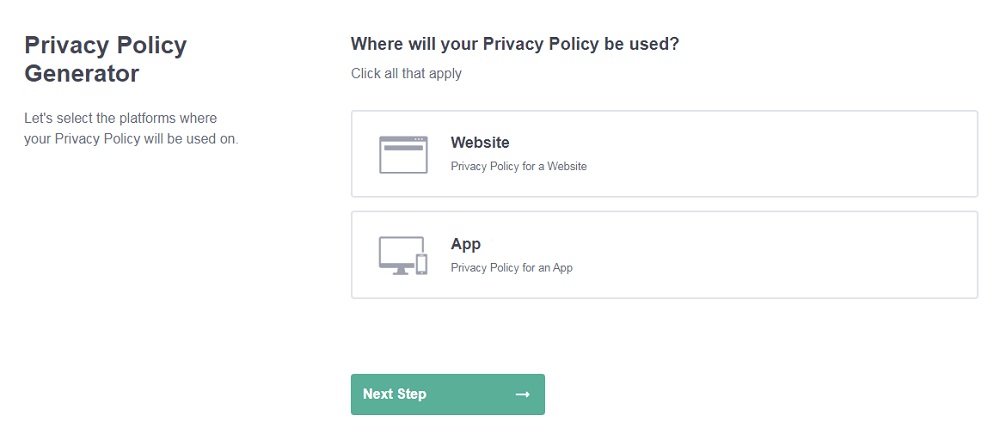
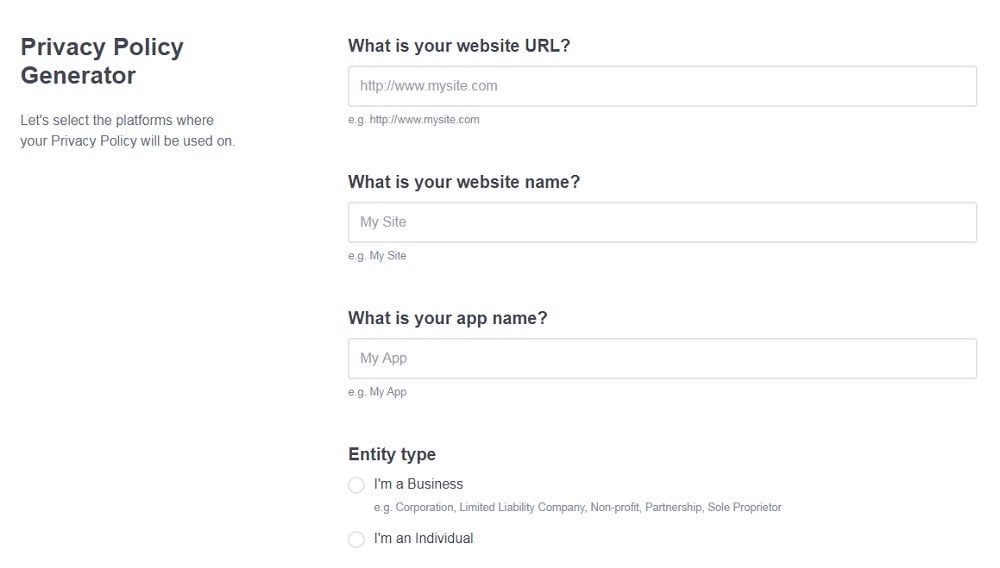
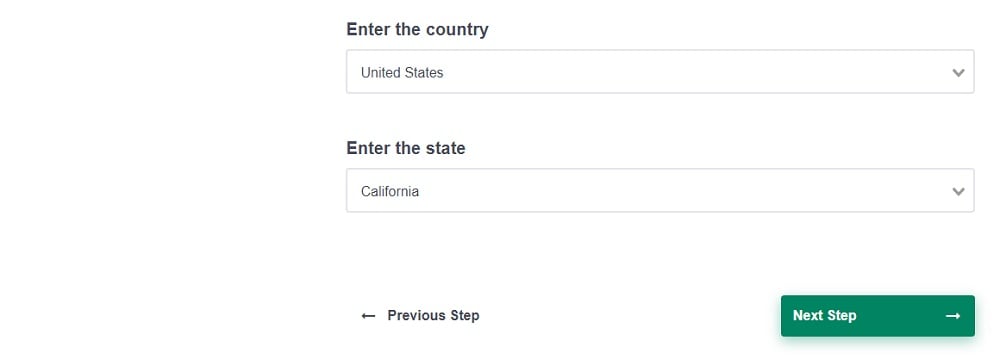
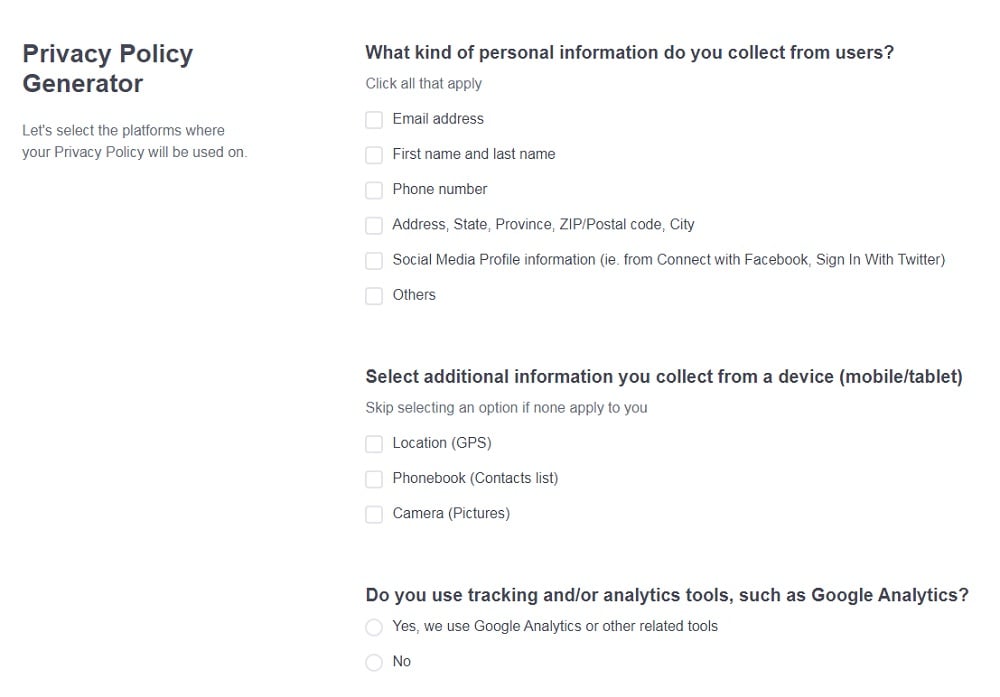
Need a Privacy Policy? Our Privacy Policy Generator will help you create a custom policy that you can use on your website and mobile app. Just follow these few easy steps:
- Click on "Start creating your Privacy Policy" on our website.
- Select the platforms where your Privacy Policy will be used and go to the next step.
- Add information about your business: your website and/or app.
- Select the country:
- Answer the questions from our wizard relating to what type of information you collect from your users.
-
Enter your email address where you'd like your Privacy Policy sent and click "Generate".
And you're done! Now you can copy or link to your hosted Privacy Policy.
- 1. Personal data
- 1.1. The GDPR's Definition of Personal Information
- 1.2. Examples of Personal Data
- 1.3. Does All Personal Data Collection Require Consent?
- 2. The Key Privacy Laws
- 2.1. General Data Protection Regulation (GDPR)
- 2.2. California Consumer Privacy Act (CCPA/CPRA)
- 2.3. Personal Information Protection and Electronic Documents Act (PIPEDA)
- 2.4. Australian Privacy Act of 1988 (APA as amended)
- 3. How Personal Data is Collected
- 3.1. Direct Collection
- 3.2. Indirect Collection
- 3.3. Third Party Collection/Sharing
- 4. How You Share and Manage Personal Data
- 4.1. Data Sharing
- 4.1.1. Third Parties
- 4.1.2. Internal Data Sharing
- 4.2. Data Management
- 5. A Guide to Privacy Law Compliance
- 5.1. Understand Data Movement
- 5.2. Have a Privacy Policy
- 5.3. Have a Cookie Policy (or Cookie Clause)
- 5.4. Get Appropriate Consent and Make Policies Visible
- 5.5. Use Encryption
- 5.6. Update and Maintain Policies
- 5.7. Check Third Party Agreements
- 5.8. Use Back-End Privacy Controls
- 6. Conclusion
Personal data
Privacy laws all over the world place various obligations on you. If you collect any personal data online, you must:
- Draft a Privacy Policy and sometimes a Cookie Policy
- Publish these Policies clearly on your website
- Get a consumer's informed consent to collecting and using their personal data
- Outline how a consumer can opt out of data sharing
- Have a contingency plan in place for how you'll handle a data breach if it arises
If you don't comply with the rules, you could be subject to financial penalties, other commercial sanctions, and reputation damage. Managing your obligations ultimately comes down to:
- Knowing what personal data you are collecting
- Understanding how it's collected, handled, and stored
- Asking for consent when it's necessary
- Respecting a consumer's decision to withhold data or revoke consent
So, what is personal data, and why does it matter?
Personal data is any information that can be used to personally identify an individual. Its standard definition has been set out in one of the world's leading privacy laws, the EU's General Data Protection Regulation (GDPR).
The GDPR's Definition of Personal Information
The GDPR defines personal information in Article 4. The definition is very broad and there's essentially no limit on what can be considered personal data. It all depends on whether an individual can be identified from the information:
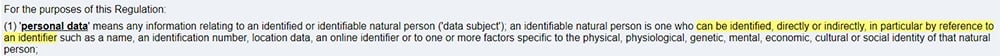
Other privacy laws define personal information in a similar way. Essentially, if it's possible to directly or indirectly identify a real person from the data in your possession, then it's personal data, it's protected under law, and you need consent to collect it.
Examples of Personal Data
While the list of what's considered personal data is non-exhaustive, it's still helpful to see some examples. Briefly, these are considered personal data:
- Name and surname
- Home address
- Location data
- IP address
- Email address
- Passport Number
- Medical data
Just because someone supplies information doesn't automatically mean that you need their consent to collect it. Some examples of data which is not protected by data protection privacy laws are:
- A company address or email address (companies are not natural persons, they're corporate bodies)
- Anonymized data
Does All Personal Data Collection Require Consent?
It's sometimes possible to collect, process, transfer, and store personal data without getting express consent. However, the circumstances are limited. Examples include:
- It's necessary to protect and preserve a life.
- You're satisfying another legal obligation that takes precedence over data privacy; for example, fraud prevention.
- You're acting entirely in the public interest.
- You need to process the data to satisfy a contract with the consumer.
Here's how Waterstones explains its right to process data to fulfill a contract:
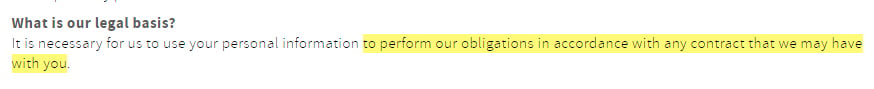
You should collect as little data as possible to perform your operations.
The Key Privacy Laws

There are four major data protection laws you should know about. If you comply with these, you're essentially complying with all your international data protection obligations.
General Data Protection Regulation (GDPR)
The GDPR is an EU Regulation on data privacy. It sets out guidelines for how businesses can collect and process personal data. The GDPR gives consumers vast new powers over what happens to their personal information and who it's shared with, and it protects every EU citizen.
Put simply, if you offer goods and services to EU citizens, you must comply with the EU's Regulation:
California Consumer Privacy Act (CCPA/CPRA)
The CCPA, or California Consumer Privacy Act, protects California residents and gives them full control over who they share personal data with, what companies do with that information, and whether companies can sell their data to third parties. It was amended by the CPRA, with the additions becoming effective January 1, 2023.
Like the GDPR, consumer consent to data sharing is critical.
If you run a for-profit business, and your gross annual takings exceed $25 million, or over 50% of your revenue comes from selling or sharingdata belonging to Californians, or you process, receive, and distribute data from at least 100,000 Californians, you must comply with the Act.
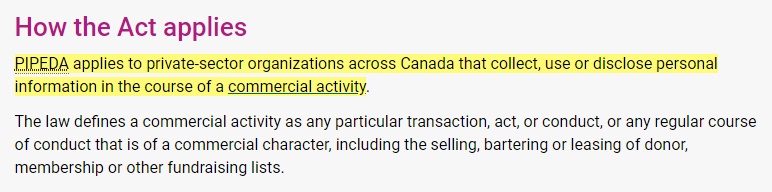
Personal Information Protection and Electronic Documents Act (PIPEDA)
In Canada, the major data protection law is PIPEDA, or the Personal Information Protection and Electronic Documents Act. The Act controls how private sector companies (i.e. for-profit companies) gather, process, share, and store consumer data, and it has far-reaching consequences for companies operating in Canada or selling goods and services to Canadian citizens.
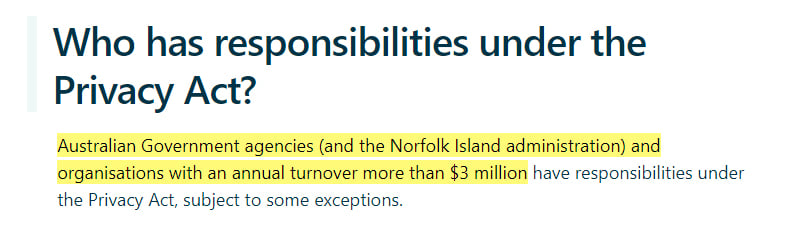
Australian Privacy Act of 1988 (APA as amended)
The Australian Privacy Act, or APA, promotes the personal rights of Australians to control who has access to their personal data, and how companies share, store, and handle sensitive information. It's based on 13 general principles, and it typically applies to Australian government organizations and private companies with an annual turnover exceeding $3 million:
Let's consider the various ways you actually collect information, and how privacy law applies to your day-to-day work.
How Personal Data is Collected

Data collection generally falls under one of three categories: direct data collection from the consumer, indirect tracking e.g. analytics, or third party sharing.
Direct Collection
If you're receiving data directly from the customer rather than, for example, through third parties or cookie analytics, it's a direct request. Examples include:
- Newsletter signups
- Account registrations
- Entering competitions
- Order placements
Indirect Collection
You can collect personal information from individuals through cookies or other analytics tracking; for example, IP information and hardware data.
Although some of this tracking doesn't always require consent, you should always tell consumers that you may gather their data this way.
Third Party Collection/Sharing
Companies can receive personal data from third parties, such as analytics providers, payment processors and email newsletter services.
DMSL helpfully sets out these three categories in its Privacy Policy:
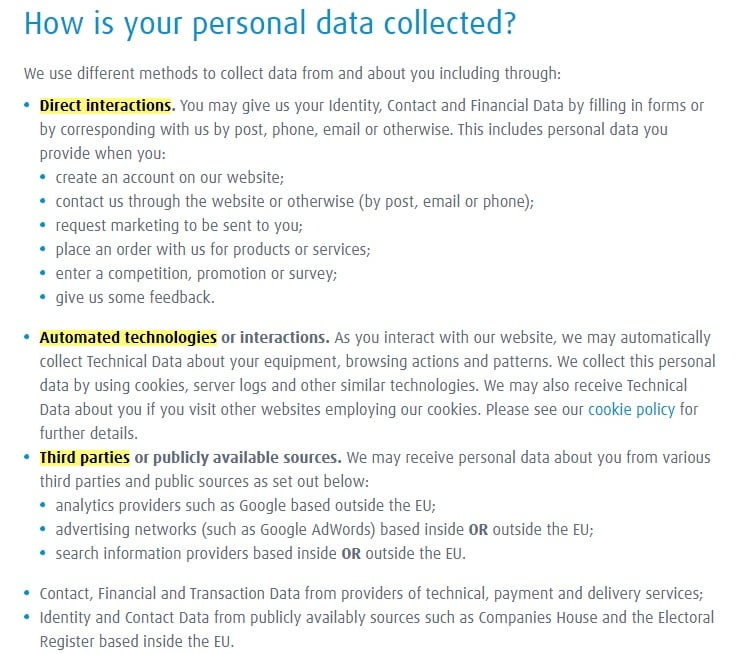
Make sure you know where all of your data comes from so that you can best protect it and accurately disclose how you collect it in your Privacy Policy.
How You Share and Manage Personal Data

It's helpful to look at the various ways companies can share and manage personal data.
Data Sharing
In most circumstances, you can't share personal data without a customer's consent. Here are some examples of when you might share data in your organization or with external parties, and what you should bear in mind.
Third Parties
You should only share personally identifiable information with third parties if there's a good reason. For example, if it's necessary to fulfill the consumer contract or deliver services.
The individual should consent to the sharing, and as mentioned above, you should only share the minimum required data. This is known as data minimisation in Article 5 of the GDPR:
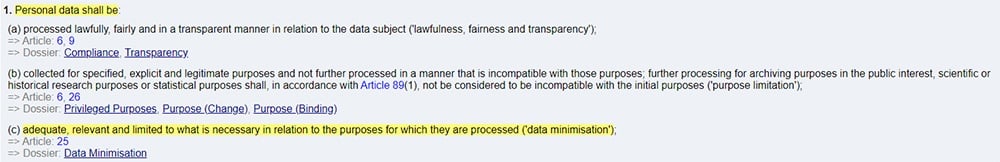
Internal Data Sharing
If you're sharing data between employees or departments, the same rules apply. The data must be handled with care and some employees shouldn't have access to information they don't need, or data that's potentially sensitive and confidential.
Data Management
It's important that you manage your data sharing and data collection strategies. Some examples of how you can manage data properly include:
- You appropriately train employees.
- You have a process for documenting what information has been collected, what information you're allowed to share, and who you've shared it with.
- You know how you'll erase data securely when you're no longer entitled to hold it.
- You have procedures in place for dealing with data breaches.
A Guide to Privacy Law Compliance

Let's consider how you can comply with your regulatory obligations by looking at some examples.
Understand Data Movement
You must know how personal information moves around your organization, whether it's internally or whether it's transmitted to third parties. To stay compliant, ask yourself these questions about any data you receive and get clear answers:
- How was this information gathered?
- What data has been collected?
- Why has the data been gathered?
- How is the data stored, and how is it processed?
- Where is the data shared?
- How is the data erased?
If you don't have clear answers to these questions for all data in your possession, you need to revisit your privacy compliance.
Have a Privacy Policy
Every website that gathers personal data from customers and other individuals must draft and publish a Privacy Policy on their website. A Privacy Policy must explain:
- You collect personal data
- Your legal basis for collection
- What type of data you collect
- How you collect it
- What you do with it once it's in your possession
- Who you share it with
- How people can opt-out of marketing and analytics
- Who people can contact with any questions and to find out what data you have on them
Here's an example of a relatively straightforward Privacy Policy from Levi's. First, it sets out how it collects data, and the categories of data it collects:
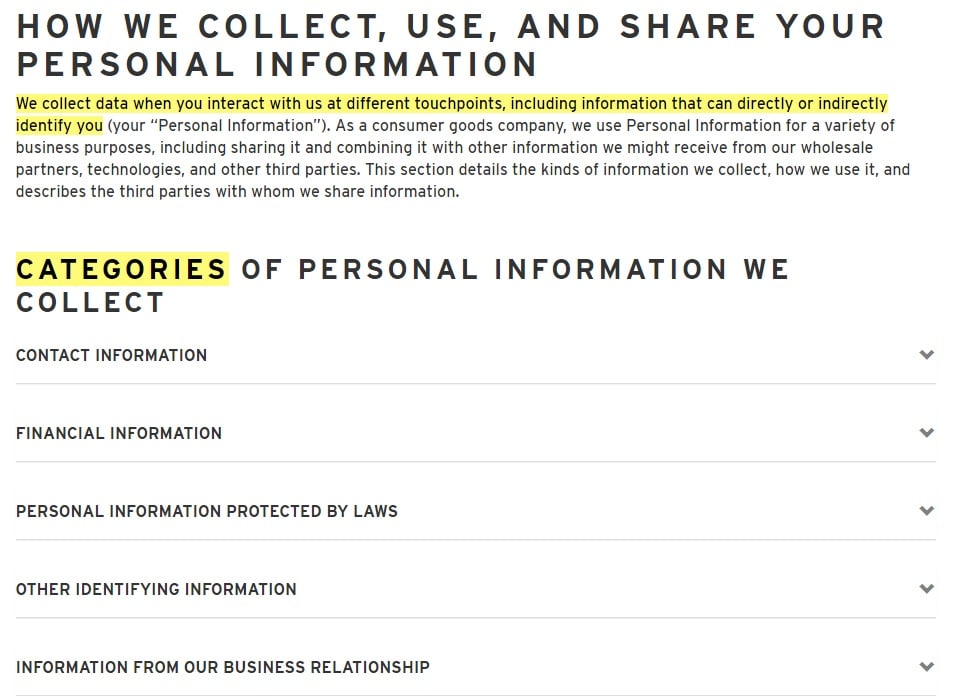
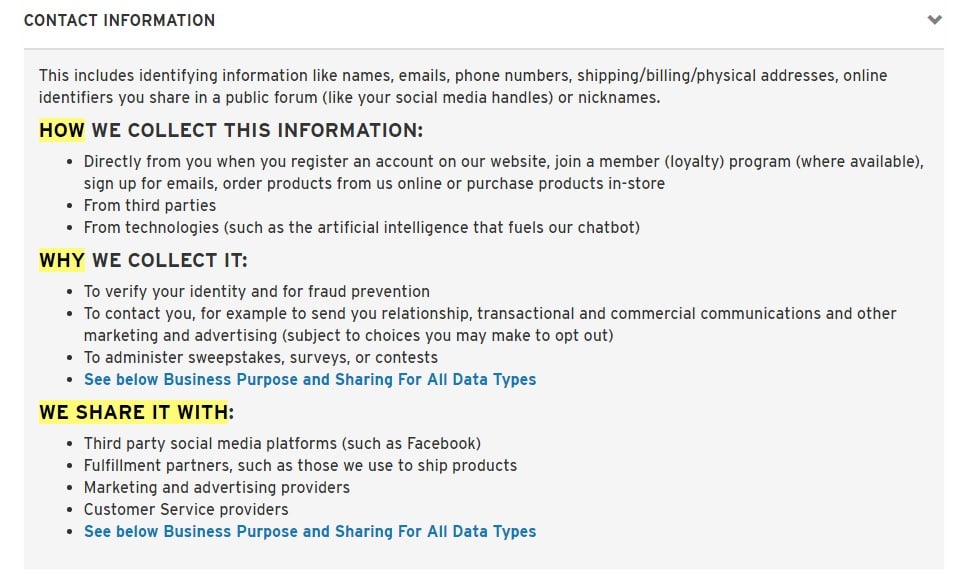
It sets out specifically how contact information collected, why, and who it's shared with:
It also sets out a person's rights and choices:
A contact information clause with numerous ways for people to contact the company for further information is also included:
Have a Cookie Policy (or Cookie Clause)
You can either include your Cookie Policy as part of the Privacy Policy or set it out separately. It should include:
- A disclaimer that you use cookies
- What cookies you use
- Why you use cookies
- How cookies are managed
- How users can opt out
- Where people can find out more about cookies
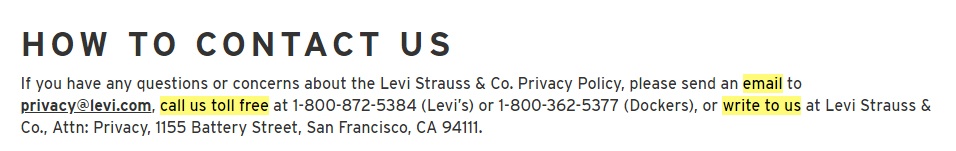
Here's how the Gymshark Cookie Policy looks, with a general informative paragraph followed by drop-down boxes with more detailed information for each heading:
You can include this same information in your Privacy Policy if you aren't legally required to have a separate Cookie Policy.
Get Appropriate Consent and Make Policies Visible
Whenever you request consent, it's best to ask for it in the most clear way and have your users take some sort of action to show consent. For example, you can use the following things when requesting consent:
- Unticked checkboxes
- Clearly-labeled buttons
- A combination of both
John Lewis uses a button that uses the words "Allow all" to get consent for cookies. This is good since people can't really argue that they didn't consent to allow cookies if they click something that says "Allow."
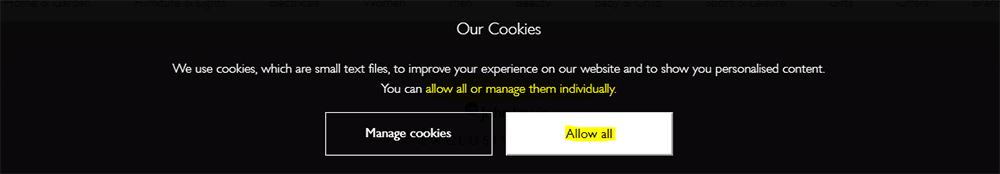
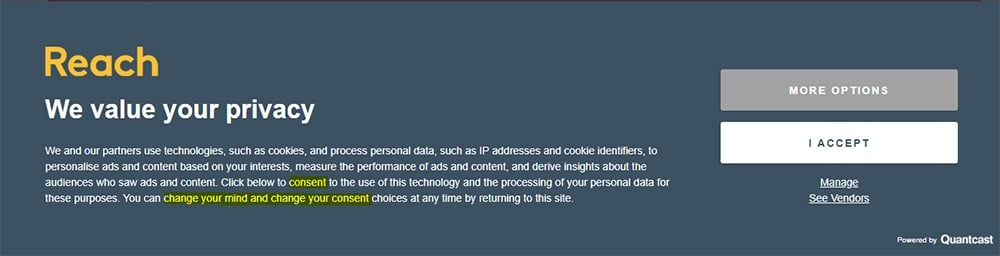
UK newspaper, the Daily Record, has a more comprehensive example of a cookie consent notice. Its consent request form tells visitors:
- How cookies are used
- What visitors are consenting to if they continue using the site
- How visitors can amend their consent settings if they deem it appropriate
Here's an example from retailer, Tesco. It uses a pop-up checkbox at the top of the website that highlights the Cookie Policy and Privacy Policy. By clicking on "accept" on the bottom right hand corner, you're consenting to the terms of these policies. You'll see that there's also a clickable link to the Privacy Policy so that visitors can read the policy in full before consenting:
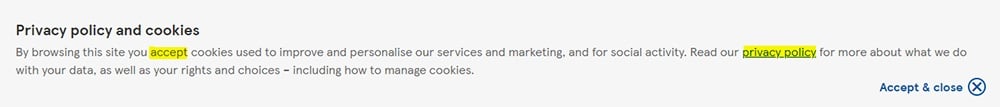
To fully comply with GDPR, express consent to personal data collection is best.
Put links to your policies in the header, footer, or sidebar. It's a good idea to link to them in your checkbox or cookie consent notices like the examples above, as well as in other places like checkout pages, sign-up forms, etc.
Here's a few examples so you can see what these links look like. First, here's an example of Privacy Policy and Cookie Policy links in a website footer at Gymshark:
![]()
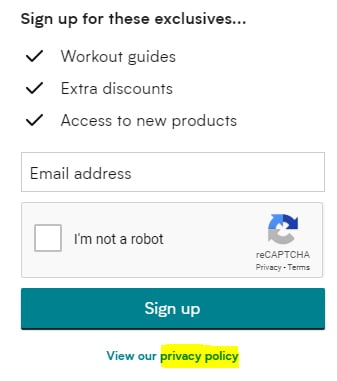
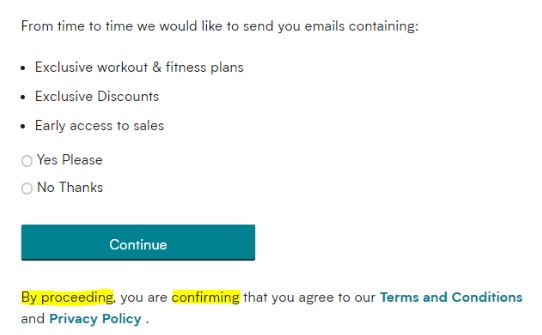
If you want to use popups to encourage visitors to sign up for an account, or sign up for your newsletter, it's a good idea to link directly to your Privacy Policy at this stage so they can review it before supplying you with information.
Here's a popup from MyProtein. Before users sign up for a newsletter and other promotional features, they have the chance to review the Privacy Policy in full:
Let's stay with MyProtein and follow its steps to create a customer account. If users proceed with making an account, they're given the chance to review the Terms and Conditions and Privacy Policy first. MyProtein can assume that users read and consented to these policies before creating their account:
Another key place you should include links to your Privacy Policy and Cookie Policy is the checkout screen. Users should understand why you need the information they're supplying, and how you plan on using that information, before they complete their transaction.
Here's an example from Bulk Powders. By submitting their data, users are agreeing to how the payment handler, Klarna, collects, uses, and processes information, and they're also agreeing to Bulk Powder's Terms and Conditions:
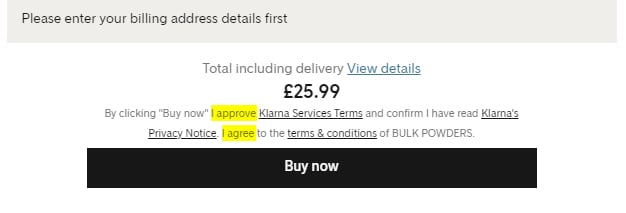
What's important here is that you regularly draw attention to your Privacy Policy and/or Terms and Conditions. This is an easy way to comply with privacy regulations.
Use Encryption
The GDPR's Article 32 confirms that you must have secure ways to manage and process data. One of the most popular (and cost-effective) ways to securely process data is encryption:
Encryption lets you "mask" or "scramble" data so that only authorized personnel can access it, which protects against unauthorized access to personal data.
To encrypt data properly, ensure you:
- Choose the right key size and algorithm
- Educate staff how to use it correctly
- Be aware of any sector-specific guidance, and how it applies to you
Update and Maintain Policies
Update your Privacy Policy and Cookie Policy at least every 12 months. Notify users when you make changes to your policies so they can familiarize themselves with any new clauses. If they continue using your website, it's implied they consent to the changes.
If you're expanding how you handle, collect, or share personal data, get updated consent.
Check Third Party Agreements
Check your third party vendor agreements for privacy law compliance. What you need to check varies by agreement, but essentially, ensure that:
- The vendor must notify you as soon as possible if there's a data breach
- They must cooperate with you to remedy the breach and notify affected individuals
- The vendor's security processes, such as encryption, are sufficient
- They can demonstrate their commitment to data privacy compliance
If you haven't updated your third party agreements since the GDPR and CCPA (CPRA) rolled out, you should do so now.
Use Back-End Privacy Controls
The back-end is the parts of the website that individuals don't see. It's the server, or the database where you store information. Privacy laws oblige you to properly safeguard gata in your possession, whether it's transferred through your server, or stored in a database.
If there's a data breach, it's your responsibility to show you took reasonable steps to protect data, even if the breach stems from a third party you share data with. Comply with privacy laws by:
- Using encryption or indexing
- Limited authorized access
- Separate your processes so that a hacker who access the front-end can't automatically access the back-end
- Updating your server and database at regular intervals
- Showing you have a response plan that enables you to react to data breaches and remedy them without undue delay, and that you have processes in place for contacting affected users and appropriate authorities
Conclusion
Every website that uses cookies or collects personally identifiable information must comply with various international privacy laws, including the GDPR, CCPA (CPRA), PIPEDA, and APA.
You are responsible for properly safeguarding this personal data, storing it securely, and only sharing it with parties you have permission to share it with. It's also your responsibility to delete data if a person asks you to do so, and to ensure that your third party vendors have stringent, secure compliance policies in place.
Comply with your obligations by:
- Creating Privacy and Cookie Policies
- Publishing them on your website and including clear links to them
- Getting express and informed consent to data collection
- Updating your Privacy and Cookie Policies at least every 12 months
- Storing data safely using encryption or similar techniques
- Training your staff on good compliance practices
- Responding to data breaches without undue delay


