How to Conduct a Data Protection Impact Assessment
Of the many new measures imposed by the General Data Protection Regulation (GDPR), the requirements surrounding Data Protection Impact Assessments often cause the most confusion. Many business owners have no idea what the document is for or when it is required.
In this article, we'll wade through the legalese to explain the complexities of Data Protection Impact Assessments so you can do your own successful assessment and document it in the best way possible.
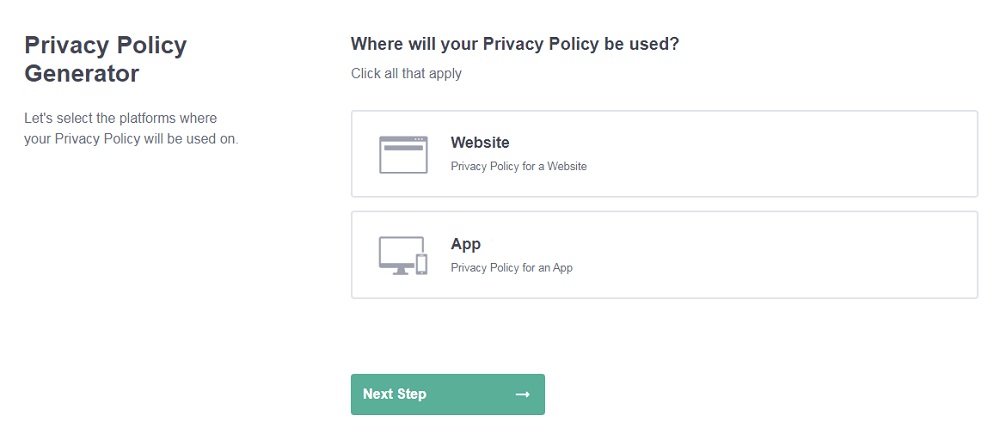
Need a Privacy Policy? Our Privacy Policy Generator will help you create a custom policy that you can use on your website and mobile app. Just follow these few easy steps:
- Click on "Start creating your Privacy Policy" on our website.
- Select the platforms where your Privacy Policy will be used and go to the next step.
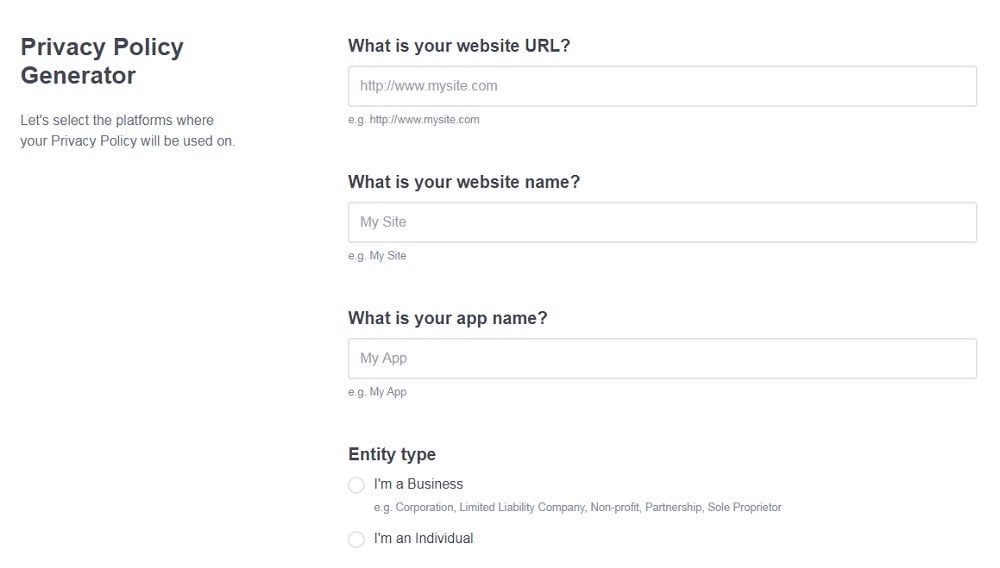
- Add information about your business: your website and/or app.
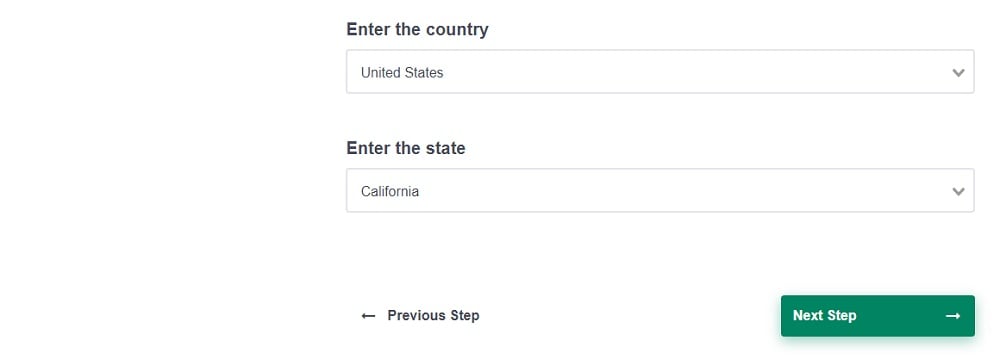
- Select the country:
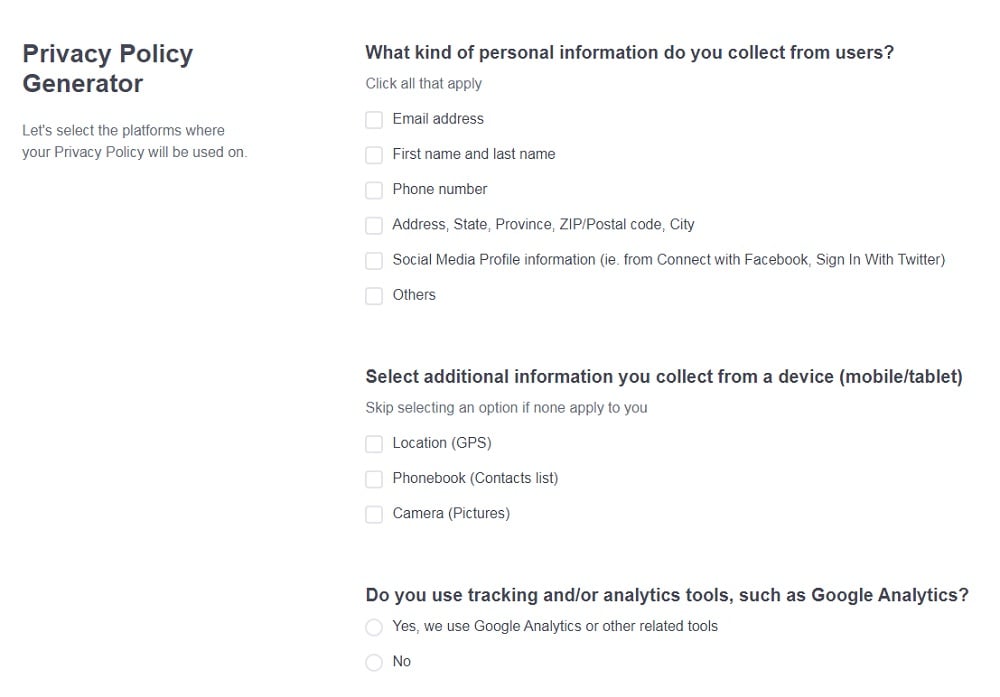
- Answer the questions from our wizard relating to what type of information you collect from your users.
-
Enter your email address where you'd like your Privacy Policy sent and click "Generate".
And you're done! Now you can copy or link to your hosted Privacy Policy.
- 1. What is the Purpose of a Data Protection Impact Assessment?
- 2. When is a Data Protection Impact Assessment Necessary?
- 2.1. When is a Data Protection Impact Assessment Not Necessary?
- 3. How to Perform a Data Protection Impact Assessment
- 3.1. 1. Describe Data Flows
- 3.2. 2. Data Scope
- 3.3. 3. Purposes of Data Processing
- 3.4. 4. Context of the Processing and Data Subjects
- 3.5. 5. Document Proper Consultation
- 3.6. 6. Specific Compliance Measures
- 3.7. 7. Identify and Evaluate Data Protection Risks
- 3.8. 8. Risk Mitigation Strategies
- 3.9. 9. Approval & Sign-Off
What is the Purpose of a Data Protection Impact Assessment?
Data Protection Impact Assessments (DPIAs) are used to investigate, recognize, and mitigate potential risks to data before launching a new business endeavor or project.
By performing a DPIA before a new project, you can hope to:
- Better understand the data protection risks that will be faced during the project
- Calculate methods to decrease or eliminate those risks
- Decide if the benefits of the project outweigh data protection risks
- Prepare an informed statement that will disclose the risks to any individuals who will be affected
- Document data protection measures to demonstrate GDPR compliance to supervisory authorities
- Identify opportunities to incorporate "Data Production by Design" principles into the project
When is a Data Protection Impact Assessment Necessary?

According to Article 35 of the GDPR:
"Where a type of [data] processing.. is likely to result in a high risk to the rights and freedoms of natural persons, the controller shall, prior to the processing, carry out an assessment of the impact of the envisaged processing operations on the protection of personal data."
In other words, if the project presents a high risk to personal data protection and privacy, then a DPIA will be necessary.
But how does one determine what presents a "high risk"? The GDPR and the Article 29 Working Party provide some examples of projects that would definitely call for a DPIA:
- An extensive evaluation of consumer information in which decisions are made based upon automatic processing and profiling. Example: A technology that uses a person's financial history to automatically determine whether or not that person is eligible for a mortgage.
- Processing special categories of data (sexual orientation, race, religion, etc.) or criminal offense history. Example: A job board website that collects racial information or criminal history from consumers who wish to apply to online jobs.
- A systematic monitoring of a public area on a large scale. Example: Using a camera placed on a public road to record and monitor driver behavior.
- Evaluation or scoring of individuals, including profiling and predicting. Example: An internet technology that monitors user behavior and uses that information to build marketing profiles.
- Automated decision-making with legal or otherwise significant effect on the lives of individuals. Example: A computer program that uses the behavioral history of convicts to automatically determine if they will be granted parole.
- Consumer data processed on a large scale. Although the term "large scale" is not defined, an example might be an online social network with millions of users.
- Datasets that have been matched or combined. Example: Direct marketing endeavors that involve purchasing consumer mailing lists.
- Data concerning vulnerable data subjects that may be unable to provide valid consent. Example: Processing the data of children or mentally ill individuals.
- Innovative technological or organisational solutions. Example: Software that provides user access based on fingerprints or face recognition.
- When the data processing "prevents data subjects from exercising a right or using a service or a contract." Example: A credit card company using a person's credit history as a basis for denying service.
As you can see, there are a lot of different scenarios that would call for a DPIA, and this is far from an exhaustive list. There are many more situations in which a new data processing project could put data protection at risk. A good rule of thumb is, if in doubt, perform a DPIA. When it comes to data security and GDPR compliance, it's always wise to err on the side of too much rather than too little data protection.
When is a Data Protection Impact Assessment Not Necessary?
In some situations, you can definitely rule out the necessity of a DPIA. These include:
- Any new project that definitely does not entail a high risk to the rights and freedoms of consumers.
- If you have already performed a DPIA for a previous project that is very similar, you can use the existing DPIA to demonstrate adequate data protection and compliance.
- When the data processing project has an established legal basis in the EU.
- If the data processing activity is on a supervisory authority's list of permitted projects that do not require a DPIA.
How to Perform a Data Protection Impact Assessment

A DPIA should be performed after the details of a new data processing project have been established and planned out, but before the project is actually launched. The GDPR lays out some specific instructions as to what a DPIA should include:
- A detailed description of the project as well as the purpose of the project
- An assessment of the necessity of the data processing involved and on what scale
- An assessment of all possible risks to data protection and consumer privacy
- An explanation as to how those risks will be mitigated and how the project will adhere to GDPR policies
While this may look like a relatively short list, there is a lot of research and effort involved in fulfilling these requirements. Below we've laid out steps you can take to create a comprehensive Data Protection Impact Assessment.
1. Describe Data Flows
Start by describing how data will be handled throughout the project. Detail is key here, so be as thorough as possible in examining your data processing activities from start to finish.
Here are some questions to ask as you compile this section:
- How will the data be collected?
- How will the data be used?
- Where and how will it be stored?
- What is the source of the data?
- Will it be shared with any third party and if so, why?
- Which high-risk data categories or activities will be involved?
This DPIA performed by Simprints Technology begins by answering some the questions above in detail:
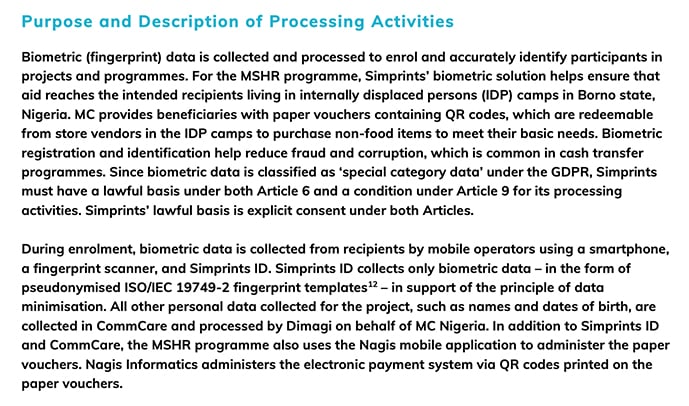
It follows this up with several flowcharts to illustrate data flows, which makes it easy to visualize and really understand what happens with data.
This section of your DPIA may be rather simple if you only work with limited data collected in limited ways, but you can see how this section could get very complicated and lengthy.
2. Data Scope
Next, outline the scope of data processing. Here you will need to delve deeply into the data itself, describing the types of data that will be collected, the quantity of data, and so on. This section will differ according the company and project involved, but may cover the following points:
- What categories of data will be collected?
- Will it involve special or sensitive categories of data?
- What quantity of data will be collected and how many consumers will be affected?
- Is the data processing localized to a specific area?
- How long will the data be retained?
Although the Privacy by Design Foundation does not go into all of these details at the outset of its DPIA, it provides a generalized scope here:
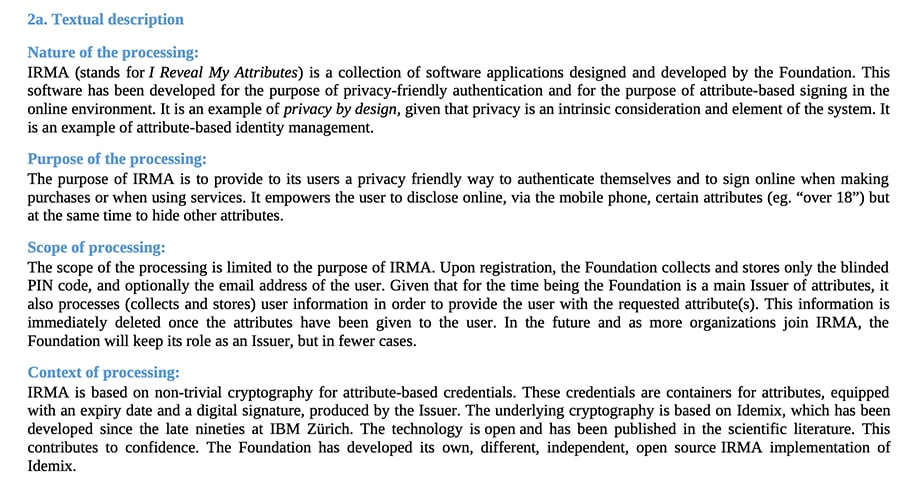
Note how the section is broken down into subsections to address things like the nature, the purpose, the scope and the context of the processing.
3. Purposes of Data Processing
Describe what the project is expected to achieve through data processing. What are the benefits for the data controller and how will consumers be affected?
UK Home Office Biometrics conducted a comprehensive DPIA to analyze new technologies to be used by the police force. This is how it describes the various purposes of the project:
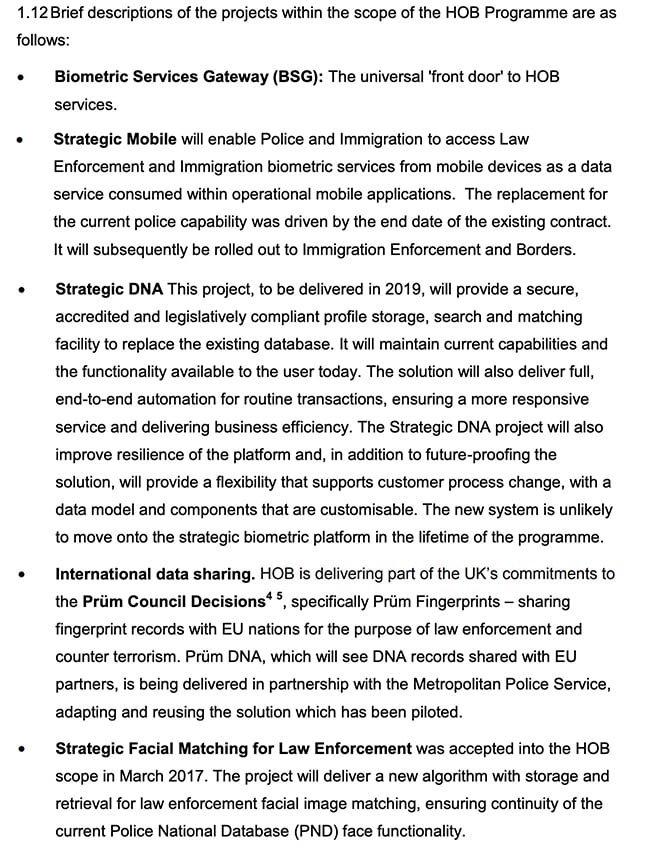
You can see how these can simply be short but descriptive paragraphs discussing the projects. The text itself notes that they are "brief descriptions of the projects."
4. Context of the Processing and Data Subjects
Here is where you start asking some of the more difficult questions. Think about the consumers who will be affected and how this data processing may affect them. This is also a good time to consider the context of the data processing project itself and its position in the industry.
Here are some questions to ask and answer during this phase:
- What is your legal basis for collecting user data? Do you have appropriate consent measures in place?
- Is your consumer base vulnerable in any way, such as in the case of children or mentally ill individuals?
- Has this type of processing been performed before? Are there similar technologies already in place?
- Have any security flaws been identified in similar projects?
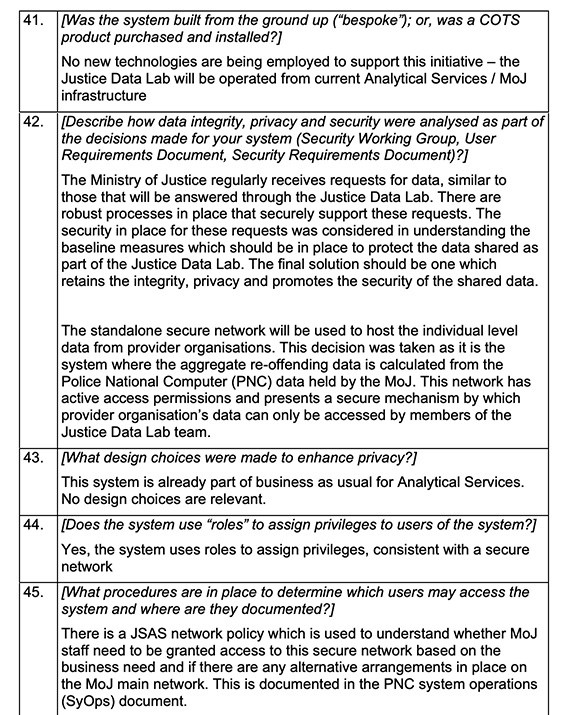
The UK Ministry of Justice employs a question and answer format for DPIAs, asking similar questions to those above in order to establish context:
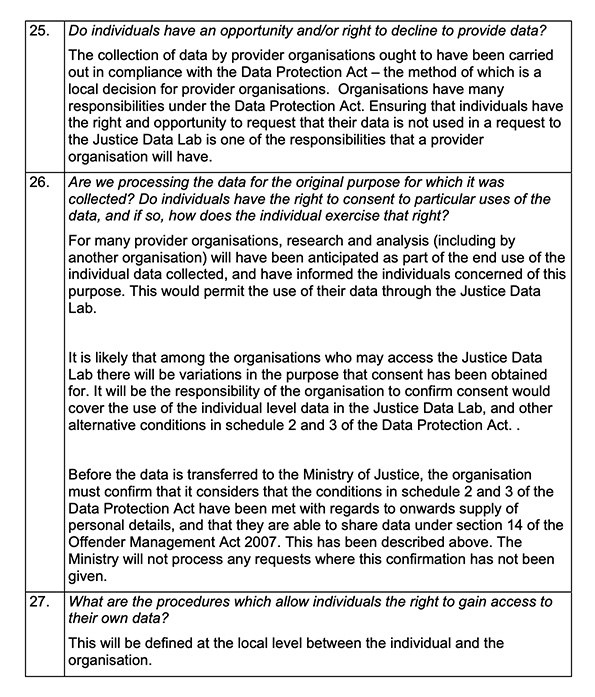
Later on in the same document, the privacy context of the new technology is also established:
5. Document Proper Consultation
Where appropriate and possible, data controllers are required to consult with consumers on their views about the new project. It may also be necessary to consult with your Data Protection Officer, data processors, or information security experts to understand the full implications and risks of the project.
If such consultations are appropriate and possible, you will need to document them in this section.
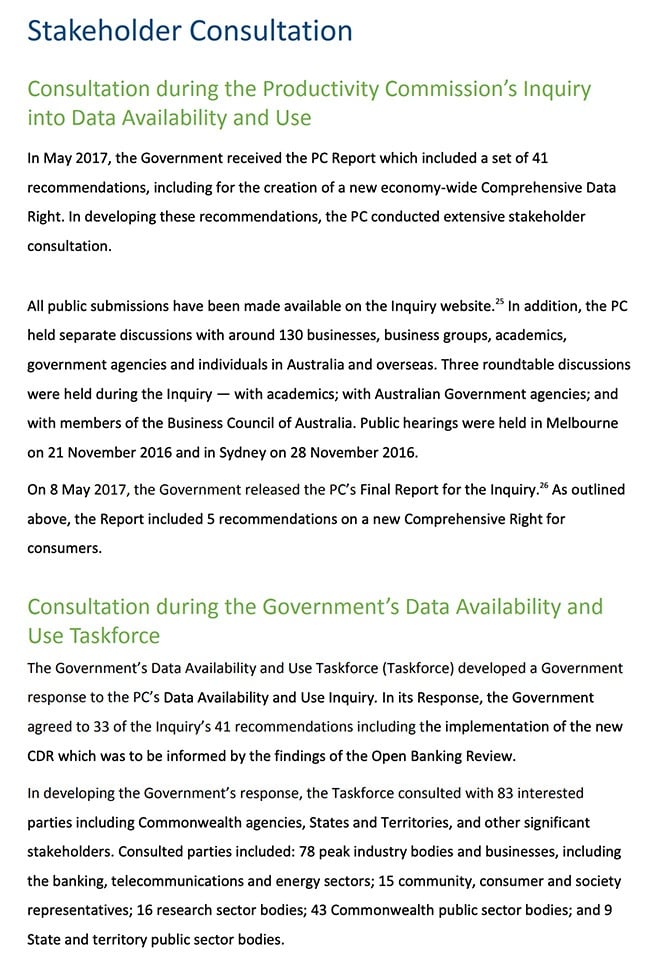
When proposing a new privacy bill to be passed into law, the Australian Department of the Treasury performed a massive 161-page DPIA to investigate all of the data protection implications that would be involved. This is a small part of the chapter discussing consultation:
6. Specific Compliance Measures
Any major data processing project will need to address GDPR compliance from the outset. After all, that's one reason you are conducting a DPIA in the first place. In this section, you will analyze whether or not data processing activities are compliant with the GDPR and other international privacy laws.
This is also a good place to describe what measures the business will be taking to ensure compliance at each phase of the project. Some topics that will need to be approached include:
- What are the legal bases for the data processing? Will these bases remain valid throughout the duration of the project?
- Is data processing necessary to achieve the overall purpose?
- Is there any way to reduce or minimize the use of consumer data throughout the project?
- How will consumer rights be upheld?
- How will the data controller confirm that third-party processors also comply with privacy laws?
- How will international data transfers be legally performed?
Simprints Technology solves this by going through the major tenets of the GDPR and briefly addressing each one:
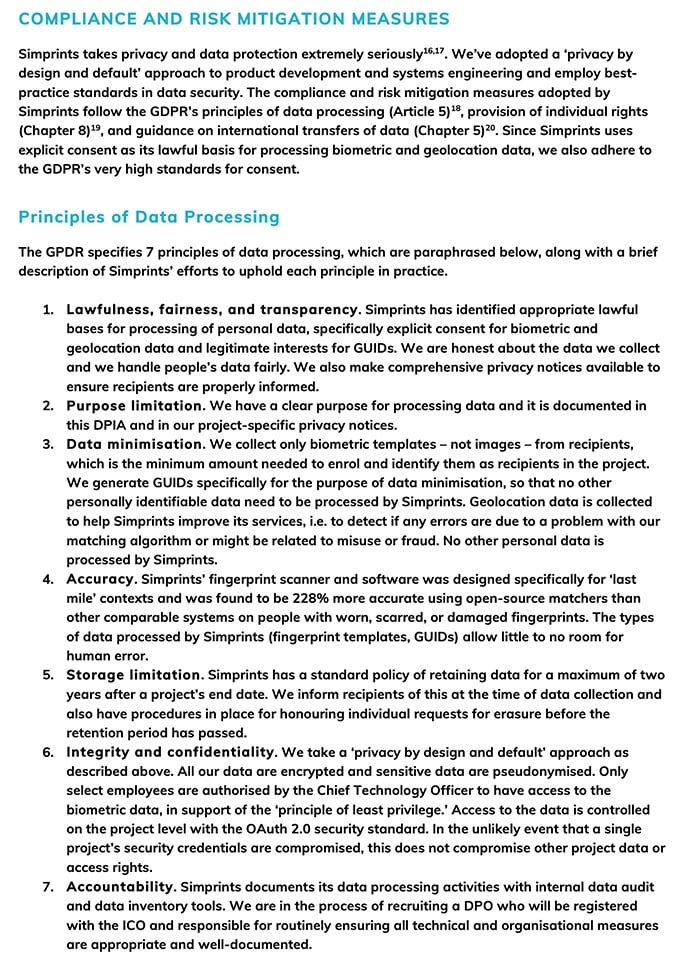
Later on in the document, data transfers and consumer rights are addressed, thereby touching on all relevant GDPR policies.
7. Identify and Evaluate Data Protection Risks
This section is considered the most important issue to explore in any DPIA. It is where data protection and privacy are analyzed from all angles. Potential threats to privacy and data security must be considered and listed.
Although it is impossible to predict every potential risk scenario in a generalized article like this one, here are some points to review during risk assessment:
- Are proper controls and safeguards in place to prevent or reduce unsafe data processing practices due to internal employee errors?
- Is there a possibility that the project might evolve and change the way data is being processed beyond the scope of current legal bases?
- Has security software been properly updated and audited against potential data theft or hackers?
- If special categories of sensitive data or vulnerable individuals are subject to data processing, is the project following GDPR-mandated stipulations to protect that data?
- Could the merging of anonymized data sets lead to individuals being inadvertently identified?
- Have data retention policies been outlined, and how will data be disposed of when it no longer serves its purpose?
- Is the information being stored in a location with adequate data security?
Of course, the potential risks to data protection will be conditional to the type of project and data processing that's involved. If you feel that your development team has not or cannot sufficiently identify potential threats to data protection, it may be necessary to consult the services of an information security expert or an attorney that specializes in privacy law.
8. Risk Mitigation Strategies
The next step is to formulate solutions and mitigation strategies to reduce or eliminate the risks identified in the assessment phase. All of the previously identified risks to data protection must be addressed in this section, as well as viable mitigation techniques for each.
Many data controllers choose to combine risk assessment and mitigation strategies into one comprehensive table that is easy to read and understand. Home Office Biometrics uses this method:
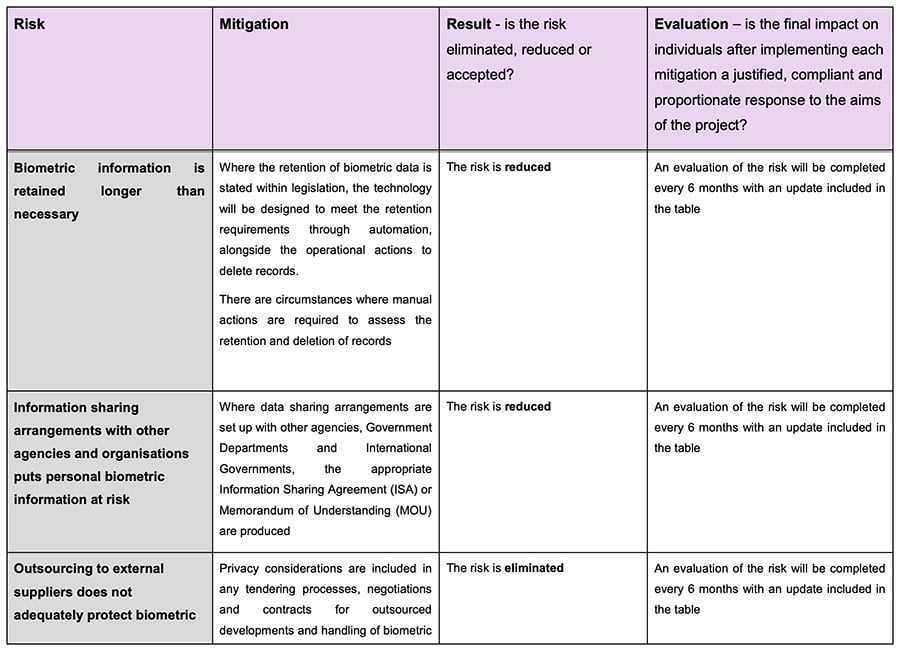
Conducting this process properly will be beneficial in the long run, especially if a privacy dispute or data incident does occur. This documentation will serve as proof that your business took every measure possible to reduce or eliminate data protection risks before the project ever launched.
9. Approval & Sign-Off
The final step in the DPIA process is to confirm that the evaluations, findings, and strategies laid out in the DPIA have been approved by the appropriate parties. The person or persons responsible for approving the document will differ according to the company and projects involved. In some cases, it may be a Data Protection Officer, while other organizations may assign approval to a management team.
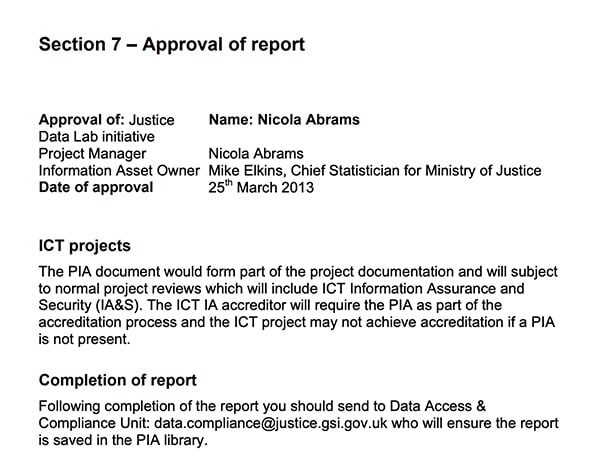
The UK Ministry of Justice requires approval and sign off by the project manager and the information asset owner:
Some DPIAs also attach a list of outcomes that resulted from the strategies suggested in the DPIA, as well as a plan of action regarding future reviews and data protection audits. These elements are not obligatory, however.
We hope that this article sheds some light on the murky, sometimes confusing process of conducting a Data Protection Impact Assessment. Following the steps above will ideally result in safer data processing practices and a GDPR-compliant approach to new projects, along with the documentation of your efforts.