How to Write an Online Privacy Policy

If your website or mobile app will be gathering any type of personal information from users for any reason, it will require a Privacy Policy.
In this article we'll cover the following information that you can refer to when writing your Privacy Policy:
- Why a Privacy Policy is necessary
- Purpose of a Privacy Policy
- Topics to include in a Privacy Policy
- Topics that apply only to specific websites or mobile apps
- Location, access and agreement
- Privacy best practices
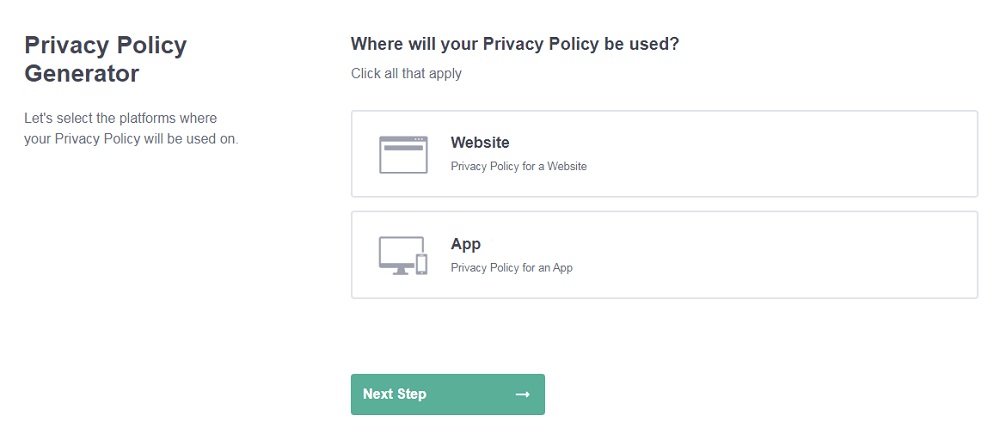
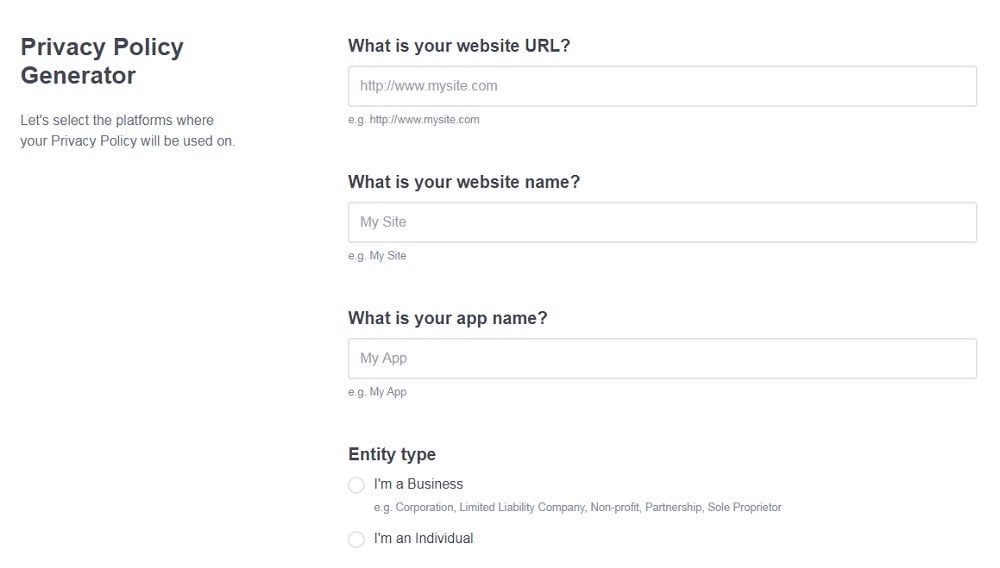
Need a Privacy Policy? Our Privacy Policy Generator will help you create a custom policy that you can use on your website and mobile app. Just follow these few easy steps:
- Click on "Start creating your Privacy Policy" on our website.
- Select the platforms where your Privacy Policy will be used and go to the next step.
- Add information about your business: your website and/or app.
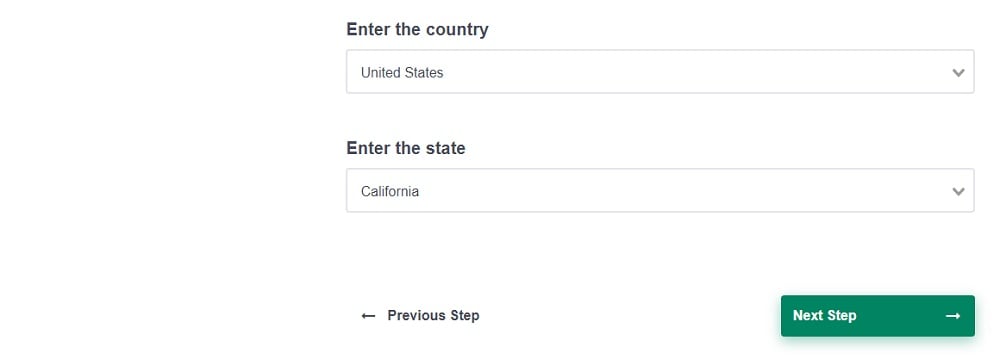
- Select the country:
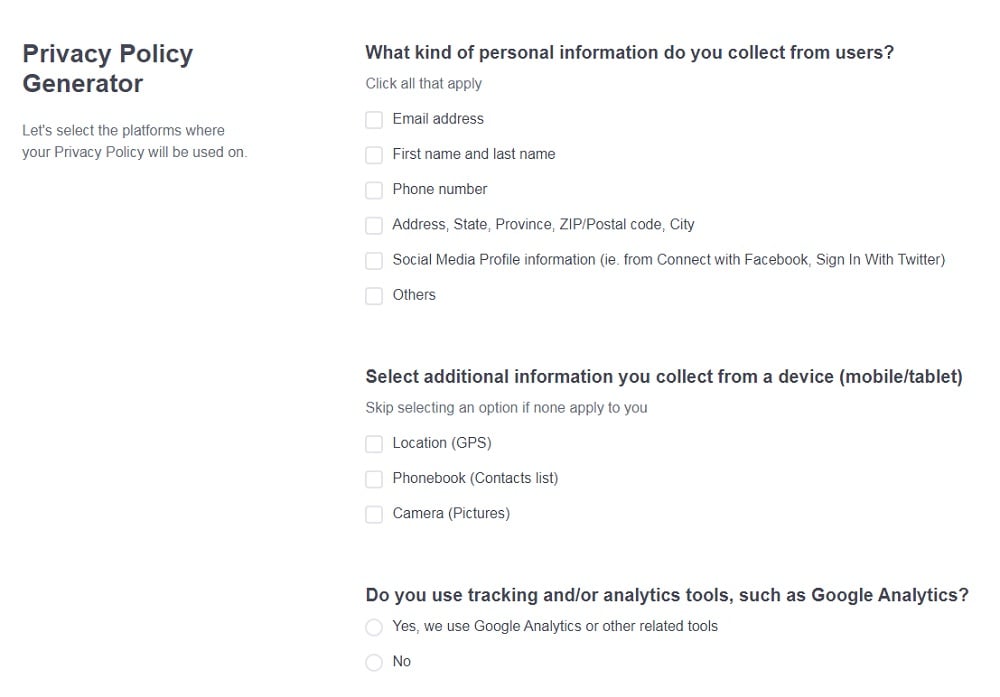
- Answer the questions from our wizard relating to what type of information you collect from your users.
-
Enter your email address where you'd like your Privacy Policy sent and click "Generate".
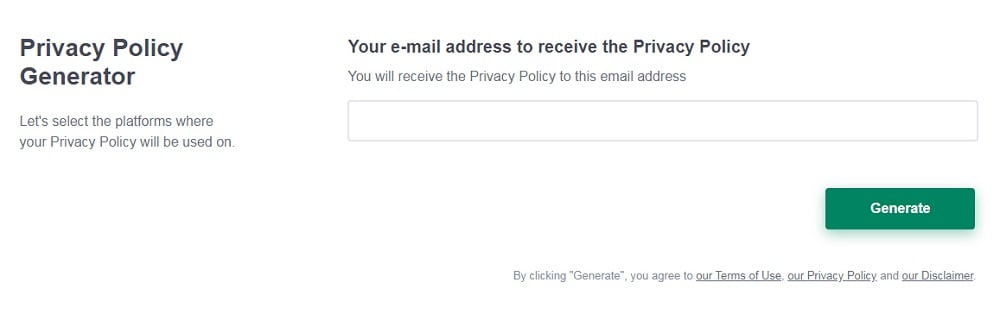
And you're done! Now you can copy or link to your hosted Privacy Policy.
- 1. Why a Privacy Policy?
- 2. The Purpose of Your Privacy Policy
- 3. Topics for Every Privacy Policy
- 3.1. Which Information is Collected
- 3.2. Methods of Collection and Data Usage
- 3.3. Children Under 13
- 3.4. Communications
- 3.5. Business Transfers
- 3.6. Dispute Resolution
- 3.7. Future Changes to Privacy Policy
- 3.8. Contact Information
- 4. Other Important Topics
- 4.1. Cookies Policy
- 4.2. Third Party Access
- 4.3. Data Retention
- 5. Location, Access and Agreement
- 6. Privacy Best Practices
Why a Privacy Policy?
It's quite possible that few users will ever read your entire Privacy Policy. You may ask yourself, is it truly necessary?
Since it will almost certainly be necessary for you to collect personal data from users, a Privacy Policy will be required by law. Several different federal regulatory systems exist to protect the privacy of internet consumers - one or all of which may apply to your business.
A few of these regulations include:
- In California, the California Online Privacy Protection Act (CalOPPA)
- In the US, the Children's Online Privacy Protection Act (COPPA)
- In Canada, the Personal Information Protection and Electronic Documents Act (PIPEDA)
- In the EU, the General Data Protection Regulation (GDPR)
Besides satisfying the requirements of international law, a Privacy Policy also helps to create an environment of transparency and honesty between you and your users. When it comes to concerns about the use of personal information online, a Privacy Policy can cultivate confidence and trust with consumers.
Lastly, a Privacy Policy can provide a handy bit of liability insurance if ever there is a dispute about the way you utilize the information you gather from users.
The Purpose of Your Privacy Policy
The general purpose of a Privacy Policy is to inform users exactly which personal information is gathered by your site or mobile app, how it is used, and how it is protected.
Here's how Zynga lays out some of the most important functions of its Privacy Policy.
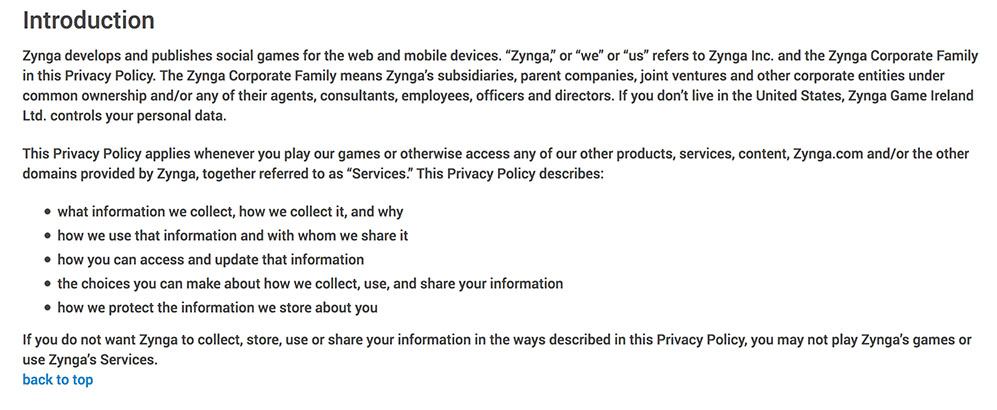
Topics for Every Privacy Policy
Although your Privacy Policy will need to be customized to fit the kind of business you are running, some topics are necessary to any website or mobile app.
Here are the basics:
Which Information is Collected
It's important to list exactly the types of personal data being collected from users, from IP addresses and email addresses, to financial and payment information. Be as detailed as possible to avoid any misunderstandings.
Instagram provides a simple list of information it collects from users:
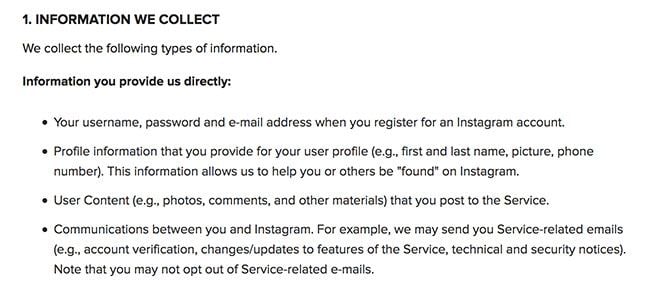
LinkedIn goes into more detail, explaining where and why information is collected:
Methods of Collection and Data Usage
Next, detail your data collection methods. This will include obvious tactics like contact forms, as well as information that your website collects invisibly on the back end, such as IP addresses and users' locations.
McAfee lists the many ways it collects information, including direct forms, automatic collection methods, and data collected from outside sources:
The second and very important part of this clause is to let consumers know exactly how you use the data in question.
Here are a few examples of how personal information might be used by your business:
- To notify visitors about important updates
- To contact customers for marketing
- Shared with third parties for analytics or advertising purposes
- To improve the content
- To display and measure ads and services
The New Scientist clearly and concisely lists all of the ways it uses personal information:
This is also a useful place to mention how important each user's privacy is to your business and how the information is protected.
Children Under 13
Whether your site is targeted to children or not, you will need a clause that addresses child privacy. Under the laws of COPPA, it may be illegal for your site to collect private information from minors without using a specific protocol to do so.
If your business is targeted to adults, then a simple statement like the one below may be all you need to limit your liability in the event that a child wanders onto your website or mobile app.
Hormel Foods issues this statement in case any children under the age of 13 try to submit personal information on their website:
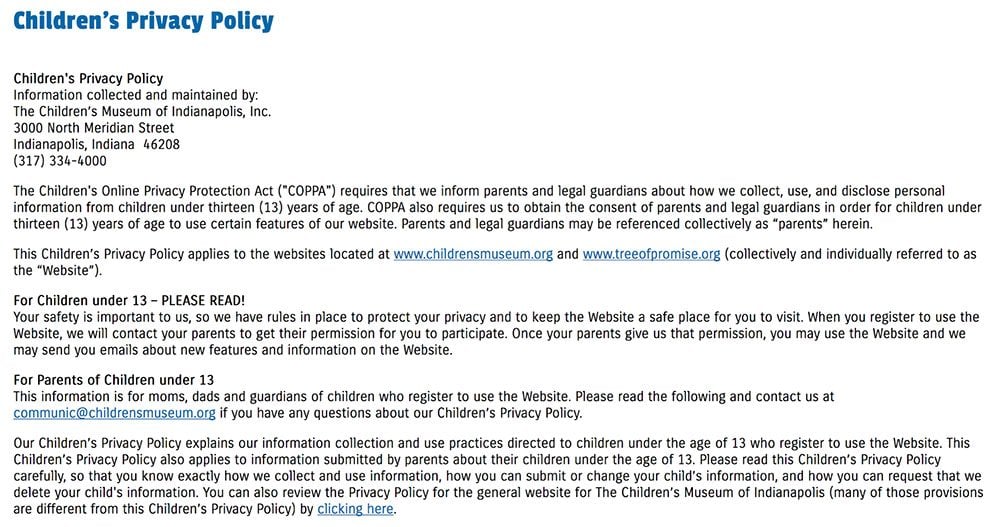
In the event that you do target teenagers or children, it will be necessary to create a more detailed Children's Privacy Policy, ideally on its own landing page. The protocol for handling children's personal information is entirely different from the protocol for adults, and it may be necessary to receive permission from parents before collecting any information.
Read more about Children's Privacy rules here.
Below you can see an example of a separate Children's Privacy Policy maintained by the Children's Museum of Indianapolis:
Communications
At some point, you will probably want to get in touch with your customers, and they may want to contact you. Because contact information includes personal information, it's necessary to include a communications clause.
GetResponse outlines what types of communication users can expect and why:
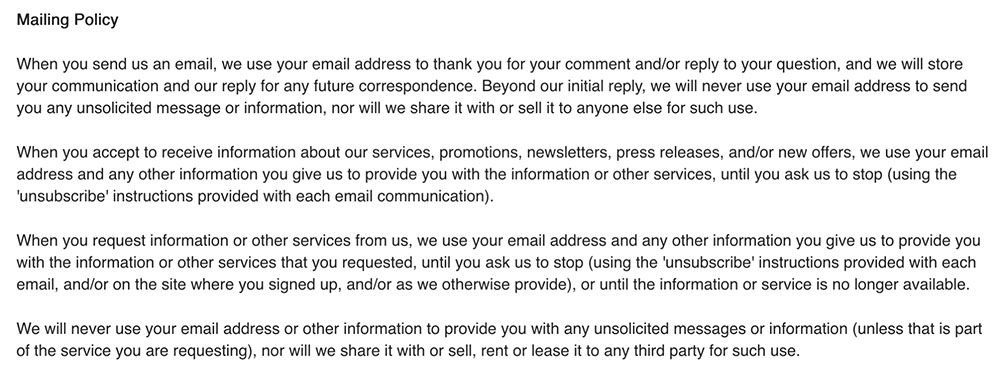
In this section, let users know how and why you plan to contact them, whether for everyday notifications, marketing, or updates on product transactions. Be sure to list the methods of communication you plan to use.
Here, Adobe explains how to adjust communications settings and opt out of communications if desired:
As demonstrated in the above screenshot, it's a good idea to let users know how to opt-out of unnecessary communications. This will help your business remain compliant with CAN-SPAM anti-spam regulations, and your users will appreciate it.
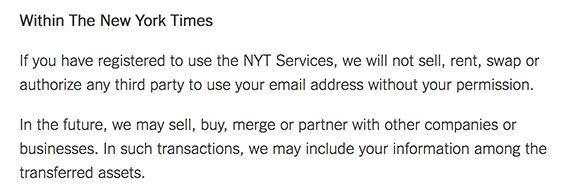
Business Transfers
Business transfers happen often and quickly. Even if you have no plans to sell your business, it's still a good idea to include a business transfer clause to limit your liability in case it does happen.
This way, users are aware that their personal information will be passed to a new owner in the event that your business is acquired by another entity.
The New York Times includes business transfer information within its Third Party Access clause:
Here is another example of a Business Transfer clause by Becton, Dickinson & Company:
Dispute Resolution
Although a more detailed outline of governing law should be listed in your Terms and Conditions agreement, a dispute resolution clause can be included in your Privacy Policy. This is simply a description of measures your business will take to resolve any future disputes.
Oracle provides clear instructions for initiating the process of dispute resolution:
This is a simpler example by AppLovin:
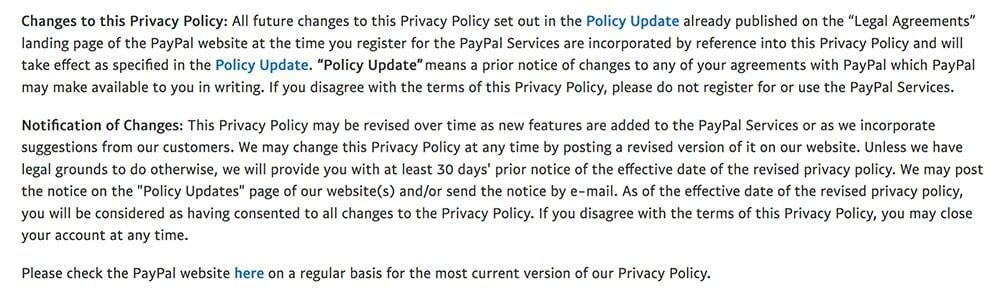
Future Changes to Privacy Policy
This section should inform users of your right to make changes to the Privacy Policy at any time, and of their right to know about it. It should let users know that they will be notified of any changes at the time the changes occur and which method of communication you will use for notifications.
AT&T efficiently describes the policy changes protocol:
PayPal goes into quite a bit more detail in its Changes to Privacy Policy clause:
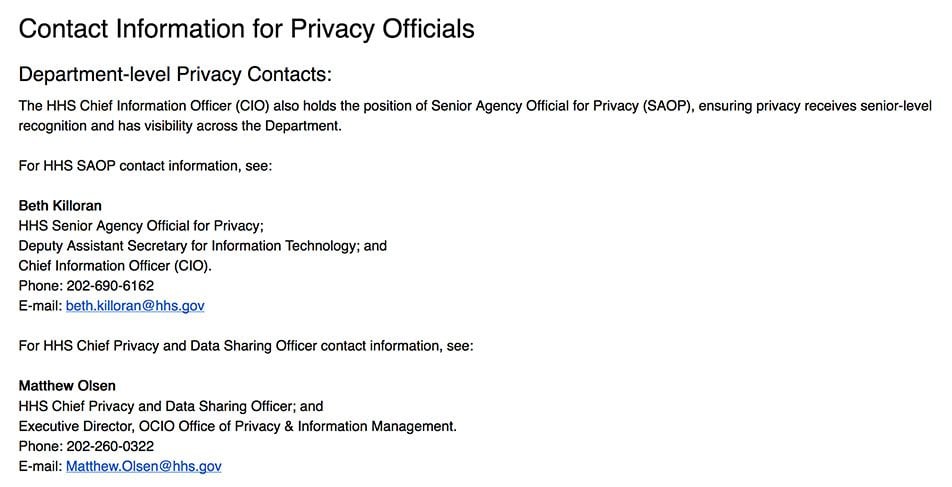
Contact Information
A contact clause adds another level of transparency for your users. Provide them with a list of ways they can contact your business with any questions or concerns about their privacy. If you can assign a specific email address and/or department to manage privacy concerns, that's even better.
Motorola provides several methods of contact within their Privacy Policy.
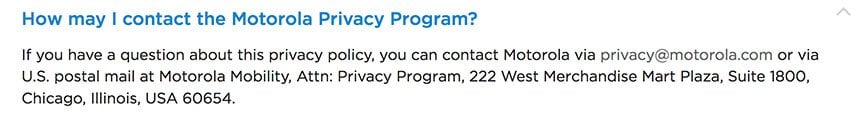
The Department of Health & Human Services provides multiple personnel devoted to privacy, as well as detailed contact information for each:
Other Important Topics
Once you've included the basic clauses that apply to any online business, you'll need to customize your Privacy Policy more specifically to your individual business.
Depending on the services you provide, the types of information you need to collect, and how the information is used, you may need to include some of the following clauses:
Cookies Policy
Although your business may not be using cookies to gather information about users, it is likely that some third party software or plugins within your website or mobile app do employ cookies.
If so, you'll need to inform users of this activity.
MailChimp includes this general cookies clause in its Privacy Policy, as well as a link to a detailed Cookies Statement.
![]()
It's a good idea to create a separate Cookies Policy to address cookies, since it can be a lengthy and detailed topic to lay out.
Here are a few things your Cookies Policy should address:
- Briefly explain what cookies are
- Describe your use of cookies and why they are necessary
- Identify which types of cookies are used by your business
- Identify the function performed by each type of cookie
Vimeo provides a link to a Cookies List in its Cookies Policy so users can see what cookies are used and the function of each:
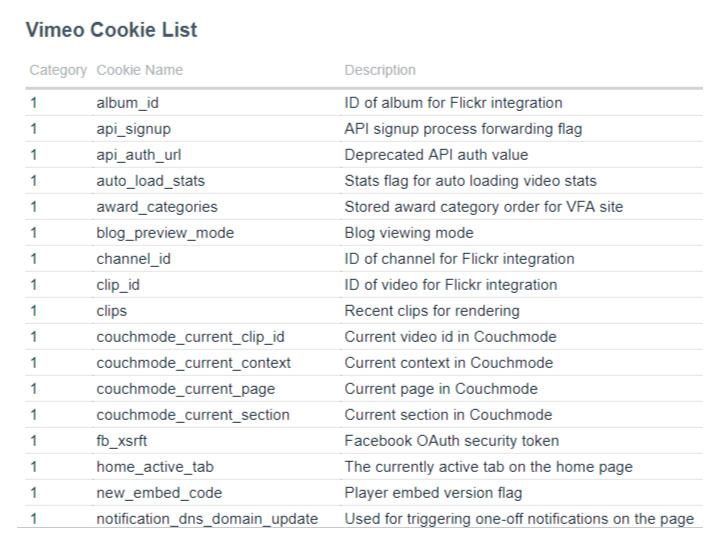
Again, it is important to include the cookies used by your third party affiliates in this list.
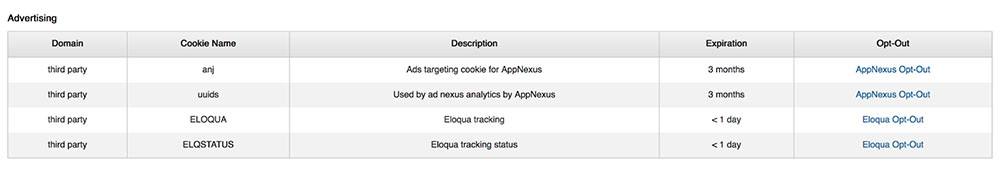
LinkedIn lists third party advertiser cookies, along with a link to opt-out for each:
Third Party Access
Most websites and mobile apps use third party affiliates to perform a variety of services for their business. These may include analytics programs, shopping cart functions, advertisers, and the like. It is probable that your business will also employ third party affiliates, in which case you will need a Third Party Access to Information clause.
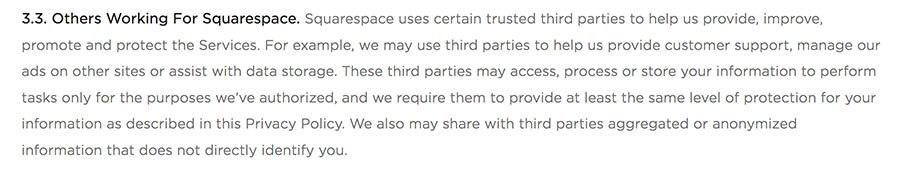
Squarespace does a good job of explaining third party affiliates, their necessity, and its commitment to information protection:
In this section, you should inform users about the existence of these third party affiliates and why it is necessary to share information with them.
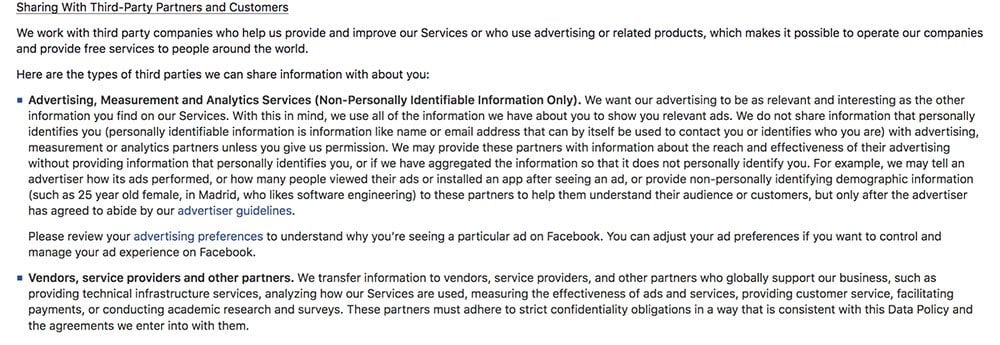
Facebook goes into great detail explaining the need for sharing information with third party partners for advertising, technical infrastructure, customer service and other important purposes:
Data Retention
For any database that allows users to set up subscriptions or individual accounts, a data retention clause will be necessary. Let users know about their right to delete their subscriptions and accounts, but inform them that some personal information may be retained on the database, even after their accounts are deleted.
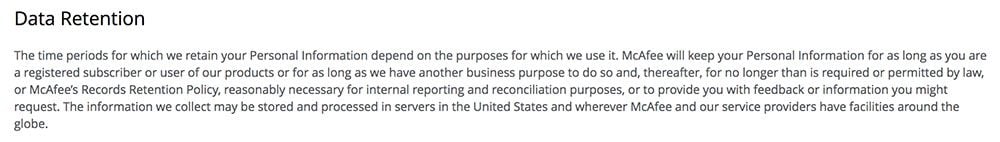
McAfee describes their policy and reasons for data retention:
Location, Access and Agreement
After you write your Privacy Policy, you're going to need to display it so users can access it easily. You'll also need to get users to agree to it to make your terms enforceable.
It's common practice to include a Privacy Policy link in clear, legible text within the footer of a website. This link usually appears alongside other important information such as contact details and other important policy links. It should appear on every page of your site or mobile app.
Twitter includes a clear link to its Privacy Policy within its website footer:
![]()
In addition to this navigational link, it is also recommended to include a link to your Privacy Policy within contact and registration forms.
On the Microsoft registration form, choosing 'Next' is an automatic agreement to the Privacy Policy. Note that links to Privacy and Cookies Statements are included:
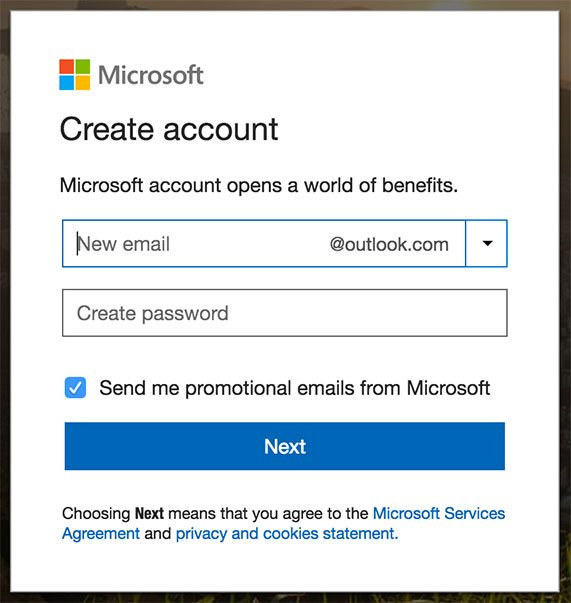
A clickwrap agreement requires users to confirm that they have agreed to the Privacy Policy before using the services on your site. This helps to ensure that your users have seen the policy and provided their consent to collect and use their data.
InstaNobel goes an extra step and asks users to click to accept the Privacy Policy before registering on the site:
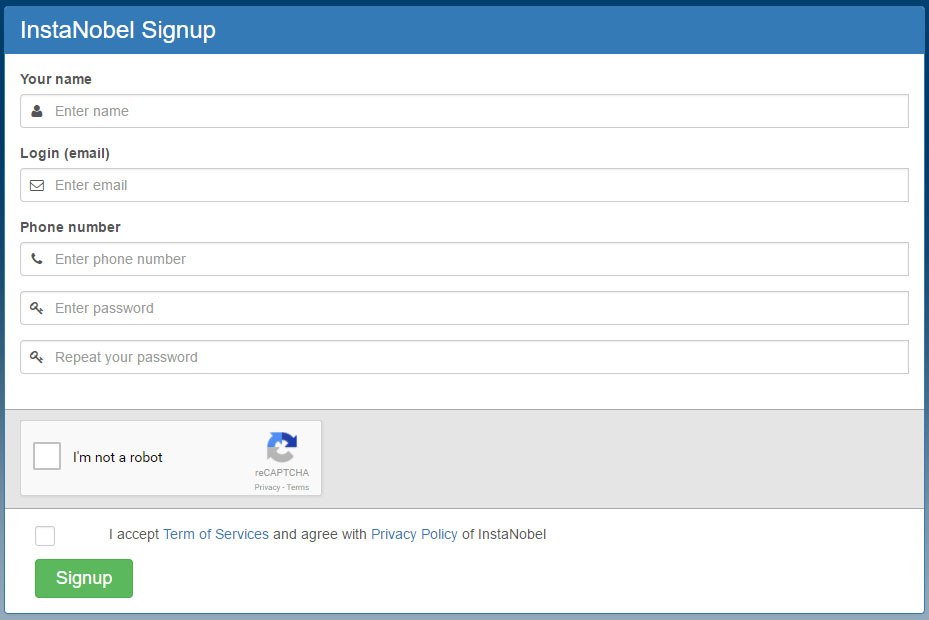
This is a great way to get users to agree to the terms of your Privacy Policy. This can help limit your liability in case a user accuses you of misusing personal information.
Privacy Best Practices
Besides your responsibility to the law, maintaining the privacy and security of your users' information is just good business.
Help make the internet a better place by following some simple best practices when writing your Privacy Policy:
- Write your Privacy Policy in plain, easy-to-understand language.
- Update your policy regularly to reflect changes in the law, in your business, or within your protocols. Notify users of these updates, and include the effective date with your policy.
- Be transparent and remain true to your commitment to user privacy.
- Make it clear and easy for users to update, change, or delete their personal information, as well as to opt-out of marketing communications.
- Make your Privacy Policy accessible and easy to find.
Writing your Privacy Policy will be easier if you take privacy seriously and understand your own privacy practices:
- Follow the FTC's recommendations and minimum regulations for protecting personal information.
- Maintain rigorous internal security measures to ensure that personal information is, indeed, secure.
- Request as little information from users as is needed to provide your services and refrain from underhanded tracking methods.